Preventing attacks on your company website: Free checklist
Start a new document with this content. Open the editor to build from scratch — paste in what you need and keep writing.
Preventing an attack on your company website checklist
Website attacks can lead to serious security breaches, disrupting operations and damaging a company’s reputation. This checklist guides organizations through the essential steps to secure their website and IT systems against common threats like hacking, viruses, and spam. It covers technical safeguards, company policies, and additional measures for data protection compliance.
Using this checklist will help you proactively defend your website, ensuring strong security practices are in place to reduce risk and support regulatory compliance.
How to use this preventing an attack on your company website checklist
To maximize protection against potential website attacks, use this checklist as a comprehensive guide. Here’s how to get the most from it:
- Follow each step systematically: This checklist is designed to help you implement robust defenses at every level of your website security. Begin by setting up technical safeguards like firewalls and virus protection, then establish internal policies and staff guidelines. Proceed through each step to build a well-rounded defense, from technology to user practices.
- Engage all relevant departments: Effective website security requires coordination across IT, HR, and management. Involve your IT team for technical setups, HR to communicate company policies to employees, and management to review insurance and recovery procedures. Cross-department collaboration ensures that security measures are consistently enforced.
- Maintain thorough documentation: Keep records of the security protocols implemented, staff training sessions, and any insurance or backup policies set up. These records are crucial for internal accountability and regulatory audits, and they help evaluate your security practices over time.
- Customize for your business needs: Adapt the checklist based on your company’s size, industry requirements, and any specific threats relevant to your sector. Businesses offering financial services, for example, may need to take extra steps to prevent phishing and secure customer information.
- Review and update regularly: Cybersecurity threats evolve, so review and refresh this checklist periodically to stay current with new threats, technologies, and compliance standards.
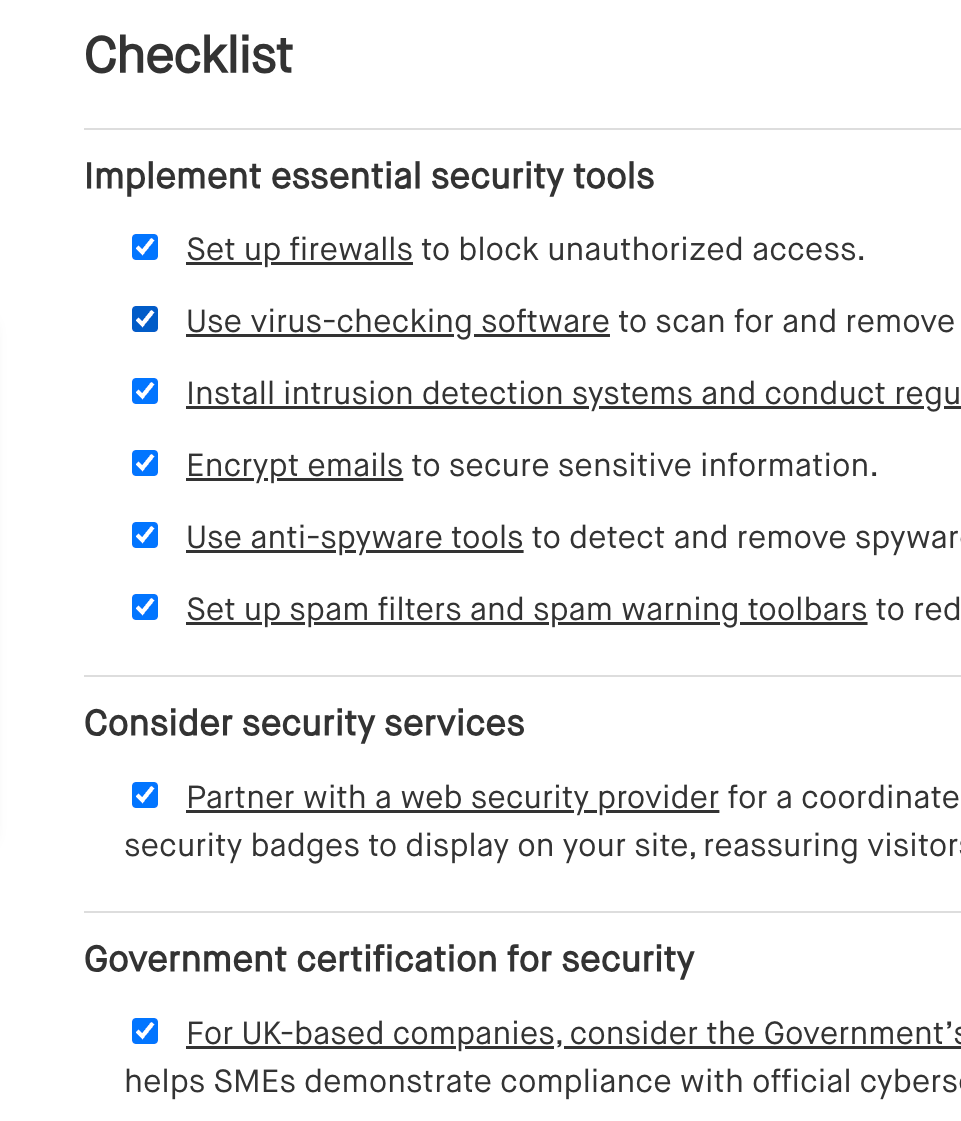
Checklist
Implement essential security tools
[ ] Set up firewalls to block unauthorized access.
[ ] Use virus-checking software to scan for and remove malware.
[ ] Install intrusion detection systems and conduct regular vulnerability scans to catch and prevent breaches.
[ ] Encrypt emails to secure sensitive information.
[ ] Use anti-spyware tools to detect and remove spyware.
[ ] Set up spam filters and spam warning toolbars to reduce spam and phishing attempts.
Consider security services
[ ] Partner with a web security provider for a coordinated setup of these security measures. Some providers offer security badges to display on your site, reassuring visitors of your protections.
Government certification for security
[ ] For UK-based companies, consider the Government’s Assurance Framework certification. This certification helps SMEs demonstrate compliance with official cybersecurity guidance.
User access control
[ ] Add a login banner on networks and restricted-access websites to inform users that only authorized access is allowed.
Prepare for emergencies
[ ] Establish backup and disaster-recovery procedures to ensure all content can be restored in case of an attack.
Establish strict security policies for employees
[ ] Prohibit employees and intranet/extranet users from importing external files or opening untrusted email attachments without first scanning them for viruses.
[ ] If software downloads are allowed, require employees to check the license terms for any references to spyware.
[ ] Define access rights clearly—inform employees about which parts of the system they may or may not access, and immediately revoke access for departing employees.
[ ] Require remote and mobile workers to install anti-virus updates and prohibit them from disabling this software.
[ ] Require employees to report lost laptops and mobile devices as soon as possible.
[ ] Prohibit employees from responding to spam, including clicking “unsubscribe” links in spam emails.
[ ] Prohibit employees from sharing work email addresses on untrusted websites or with unknown contacts.
Maintain and educate
[ ] Regularly update these security policies and provide ongoing training to ensure all employees understand and follow them.
Obtain coverage and set up recovery plans
[ ] Consider hacker and virus-attack insurance to help cover costs related to cyber incidents.
[ ] Establish thorough backup procedures to ensure that any lost data or content can be quickly recovered.
[ ] Develop a disaster recovery plan with clear steps for restoring systems and data in the event of an attack.
[ ] Regularly test backup and recovery processes to ensure they work effectively when needed.
Educate and protect customers from phishing and spoofing attacks
[ ] Instruct customers to type your website address directly into their browser instead of clicking links in emails.
[ ] Remind customers never to share passwords or PINs with anyone.
[ ] Advise customers to look for security symbols like a yellow padlock to verify secure, encrypted connections on your site.
[ ] Encourage customers to regularly check their statements and report any unusual transactions immediately.
Enforce anti-spam policies for ISPs
[ ] Require customers to prevent spam from being sent via your network by imposing contractual obligations.
[ ] Specify sanctions, such as withdrawal of email services or internet access, for breaches of anti-spam policies.
[ ] Apply these sanctions consistently, even if spam is sent from another network or through a third party.
Benefits of using a preventing an attack on your company website checklist
Using a checklist to prevent website attacks helps your organization proactively secure its digital assets, ensuring a safe experience for users and a more resilient online presence. Here’s how it benefits your business:
- Ensure compliance with data protection laws: This checklist guides you through essential security measures required by data protection regulations, reducing the risk of legal issues from data breaches.
- Streamline security processes: By following a structured checklist, you can systematically cover all key aspects of website security, from technical defenses to employee practices, ensuring no area is overlooked.
- Minimize downtime and business impact: A comprehensive approach to security reduces the likelihood of attacks that could disrupt operations or compromise sensitive data, helping maintain business continuity.
- Build trust with customers: Implementing visible security measures like encryption and secure logins demonstrates your commitment to protecting customer data, enhancing user confidence in your website.
- Prepare for potential threats: By regularly using this checklist, you keep your security practices updated, staying prepared for evolving cybersecurity challenges and reinforcing your defenses.
Frequently asked questions (FAQs)

Outlines the key factors to consider when selecting a new vendor, ensuring a thorough evaluation of their capabilities, reliability, and alignment with your business needs.
Outlines key areas for lenders to review during legal due diligence, ensuring thorough assessment of the borrower’s legal standing, risks, and obligations.

Highlights key legal considerations when dealing with user-generated content, including copyright, consent, and platform liability.