Start a new document with this content. Open the editor to build from scratch — paste in what you need and keep writing.
Responding to a data breach checklist
Data breaches can have serious consequences for businesses, from financial loss to reputational damage. This checklist helps guide organizations through the steps required to respond effectively to a data breach. It covers everything from verifying the breach, containing it, notifying affected parties, and improving security practices to prevent future incidents.
Using this checklist will help ensure your organization handles the breach professionally, minimizing risk and ensuring compliance with legal requirements.
How to use this responding to a data breach checklist
To ensure your organization manages a data breach effectively, use this checklist as a step-by-step guide. Here’s how to maximize its benefits:
- Follow each step carefully: This checklist is structured to cover every stage of the breach response. Start by verifying the breach, containing it, and notifying relevant parties. Continue through to the final post-breach review to assess security measures. Moving through the checklist in order ensures that no critical steps are missed, from legal obligations to internal processes.
- Involve all necessary departments: A data breach response requires collaboration across multiple teams. Involve your IT department to handle technical issues, legal counsel to manage compliance, PR for external communication, and HR for internal updates. Coordinating these departments ensures a unified, comprehensive response.
- Document every action: Keep a detailed log of all actions taken during the breach response. This documentation will be essential for any legal or regulatory inquiries, and it helps you track how the breach was handled at each step. Accurate records also provide valuable insights for refining your future incident response processes.
- Tailor it to your organization: While the checklist provides general guidelines, adjust it to fit your business’s specific needs. Different industries have unique legal and operational requirements, so make sure your response plan aligns with relevant laws and internal policies.
- Update regularly: Data breach risks and regulations evolve. Review and update this checklist periodically to ensure it remains relevant to new threats, technologies, and compliance requirements.
Checklist
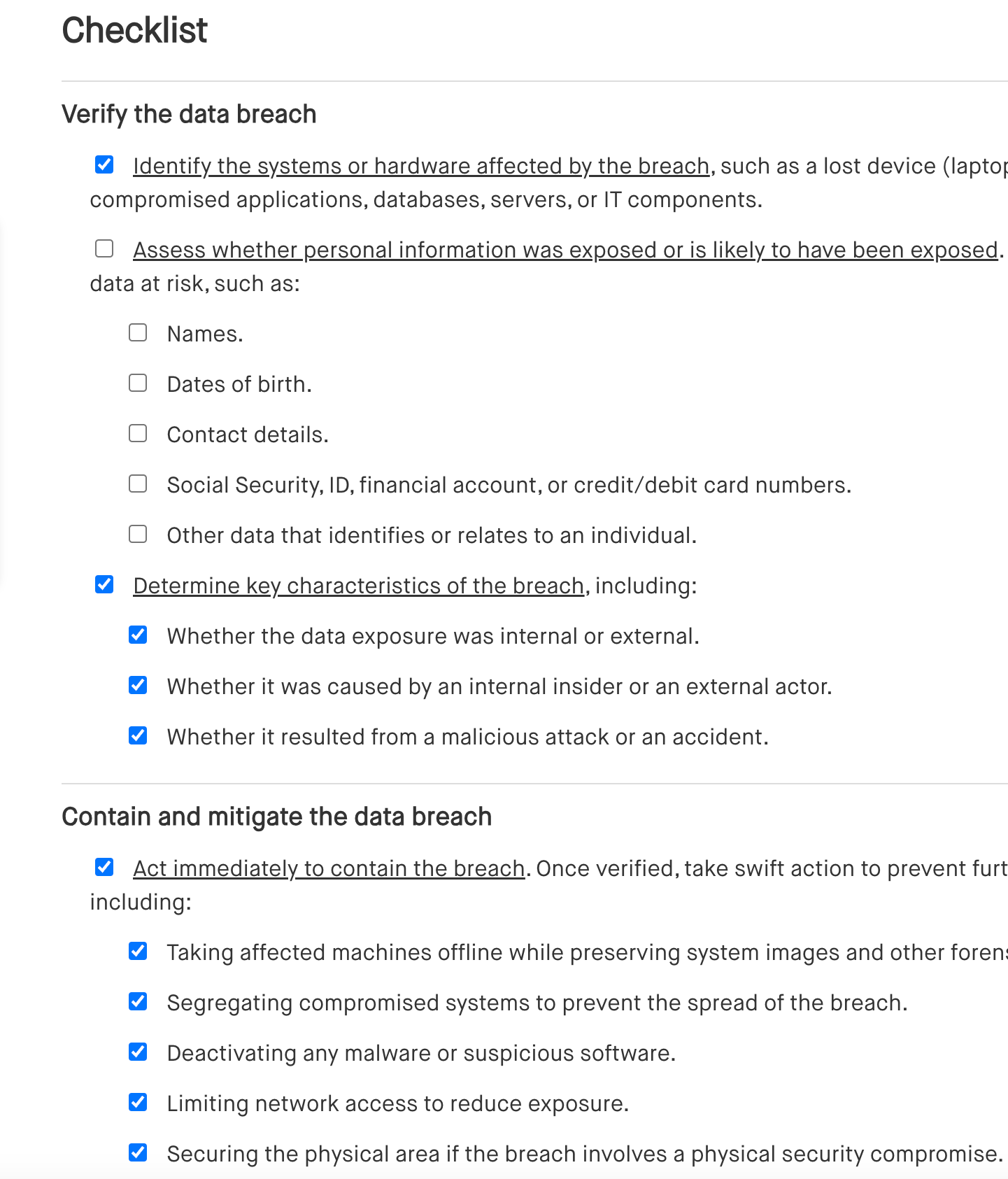
Verify the data breach
[ ] Identify the systems or hardware affected by the breach, such as a lost device (laptop, USB drive) or compromised applications, databases, servers, or IT components.
[ ] Assess whether personal information was exposed or is likely to have been exposed. If so, identify the types of data at risk, such as:
[ ] Names.
[ ] Dates of birth.
[ ] Contact details.
[ ] Social Security, ID, financial account, or credit/debit card numbers.
[ ] Other data that identifies or relates to an individual.
[ ] Determine key characteristics of the breach, including:
[ ] Whether the data exposure was internal or external.
[ ] Whether it was caused by an internal insider or an external actor.
[ ] Whether it resulted from a malicious attack or an accident.
Contain and mitigate the data breach
[ ] Act immediately to contain the breach. Once verified, take swift action to prevent further data loss or intrusion, including:
[ ] Taking affected machines offline while preserving system images and other forensic evidence.
[ ] Segregating compromised systems to prevent the spread of the breach.
[ ] Deactivating any malware or suspicious software.
[ ] Limiting network access to reduce exposure.
[ ] Securing the physical area if the breach involves a physical security compromise.
[ ] Determine if other systems are at immediate or future risk and take necessary actions to prevent additional harm.
[ ] Consider adding extra security measures such as:
[ ] Changing locks, passwords, or access codes.
[ ] Modifying administrative rights or network configurations to enhance security.
Convene the data breach response team
[ ] When a breach is suspected, gather the designated team responsible for managing the organization's response efforts.
[ ] Ensure the team follows the organization’s incident response plan.
[ ] The team should manage overall response actions, ensuring every aspect is handled according to the plan.
[ ] Investigate the breach and define the scope of the internal investigation. Collect relevant data and assess the breach’s impact.
[ ] Consider whether to:
[ ] Notify or engage outside counsel, especially if there is no in-house counsel.
[ ] Hire third-party consultants for forensic analysis.
[ ] Notify law enforcement or regulatory authorities if necessary.
[ ] Keep a response log and document all actions taken during the investigation and response process for future reference.
[ ] Implement both internal and external communication protocols to handle information flow effectively.
[ ] Conduct a post-breach review to assess the effectiveness of the response and improve future actions.
Investigate and analyze the data breach
[ ] Use in-person or telephone communications to avoid potential information leaks, especially if IT systems may still be compromised.
[ ] Conduct the investigation under attorney-client privilege where applicable to protect sensitive information.
[ ] Assess the potential legal consequences of the breach with guidance from internal or external legal counsel.
[ ] Secure all data, including forensic evidence, to ensure it is available for any future legal or regulatory action.
Collect data
[ ] Collaborate with IT or a forensics vendor and begin collecting data immediately with internal IT staff or by engaging an external forensics team.
[ ] Gather incident details:
[ ] Record the date, time, duration, and location of the incident.
[ ] Document how the breach was discovered.
[ ] Note the nature of the breach (e.g., compromised systems, lost hardware).
[ ] Determine the method of system or network intrusion, if applicable, and capture relevant details.
[ ] Establish timelines for key events like the initial compromise, discovery, and subsequent actions.
[ ] Identify which systems, files, or IT components were compromised and whether personal information was accessed or exfiltrated.
[ ] List affected personal information:
[ ] Compile a list of affected individuals.
[ ] Identify the data elements compromised and the number of records affected.
[ ] Determine if the data was encrypted and whether encryption keys remain secure or were compromised.
Analyze contract and legal implications
[ ] Assess data breach notification obligations:
[ ] Identify the types of data compromised.
[ ] Check if the data was encrypted or secured, and determine if the encryption key was compromised.
[ ] Estimate the number of affected individuals and their jurisdictions (usually based on their place of residency).
[ ] Evaluate the likelihood of harm to individuals.
[ ] Review sector-specific laws and regulations for notification obligations. Assess applicability under laws like:
[ ] HIPAA and HITECH Act.
[ ] Gramm-Leach-Bliley Act (GLBA).
[ ] Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA).
[ ] Communications Act of 1934.
[ ] State-specific health and insurance data security laws (e.g., California’s Confidentiality of Medical Information Act).
[ ] Determine notification requirements and check if applicable laws mandate notice to:
[ ] Third-party business partners or vendors.
[ ] Affected individuals.
[ ] Authorities or law enforcement.
[ ] Consumer reporting agencies.
[ ] Evaluate SEC disclosure requirements. If the organization is publicly traded, consider whether a Securities and Exchange Commission (SEC) disclosure is necessary.
[ ] Review contracts and insurance policies:
[ ] Identify obligations to notify customers, business partners, or third-party vendors.
[ ] Review insurance policies to determine coverage and notify carriers if required.
[ ] Indemnification and litigation risks:
[ ] Assess any third-party indemnification obligations or rights.
[ ] Determine if there is a risk of litigation or regulatory action.
[ ] Evaluate internal actions:
[ ] Consider actions against employees, insiders, or external actors involved in the breach, including civil or criminal remedies.
Develop a communications plan
[ ] Communicate with key stakeholders and ensure the communications plan is approved by media relations professionals, executives, and legal counsel.
[ ] Plan for the timely release of information about the breach to external parties.
[ ] Make sure all information is thoroughly vetted for accuracy and completeness before dissemination.
[ ] Develop a response strategy for handling questions from the media, affected individuals, vendors, and law enforcement agencies.
[ ] Use a structured approach for managing inquiries to ensure consistent messaging.
[ ] Adjust communication tone and content for:
[ ] Employees.
[ ] Affected individuals.
[ ] Media outlets.
[ ] Relevant vendors or third parties.
[ ] Law enforcement and regulatory agencies.
Prepare an inquiry response plan
[ ] Develop a plan for handling inquiries from affected individuals and others, that is appropriate to the size of the breach, the number of individuals affected, and applicable legal requirements.
[ ] Determine whether to handle inquiries internally or use a third-party call center or service provider.
[ ] Decide if a public statement will be posted on the organization's website (check legal requirements for this).
Consider internal communications
[ ] Limit information sharing and restrict details about the data breach to a need-to-know basis among employees and internal stakeholders.
[ ] Time internal notifications carefully. Wait until the breach is contained and the basic facts are established before notifying employees, to minimize speculation and distractions.
[ ] Assess employee impact and determine if any employees are affected individuals who must receive individual notification.
[ ] Remind employees about external communication policies.
[ ] Ensure regular updates to executives, board members, and business partners.
Plan for media communications
[ ] Hire a PR expert experienced in managing media communications during data breaches.
[ ] Minimize risk of leaks to the media before notifying affected individuals.
[ ] Draft a holding statement in advance for media response readiness.
[ ] Prepare accurate public statements based on verified facts.
[ ] Assign a team member to handle media, regulatory, and law enforcement inquiries.
Consider communications with regulators and law enforcement
[ ] Assess law enforcement contact needs:
[ ] Determine if law enforcement notification is required or recommended.
[ ] Consider delay in notification if it interferes with investigations.
[ ] Evaluate regulatory notification obligations.
[ ] Involve legal and executive teams in preparing regulatory communications.
Plan for communications with affected persons
[ ] Set up a toll-free number if required by law or appropriate.
[ ] Create a call script for staff responding to inquiries.
[ ] Train staff on escalation processes for complex questions.
[ ] Develop FAQs for affected individuals.
[ ] Update breach information on website, if necessary.
[ ] Appoint a response coordinator for handling direct inquiries.
Prepare a notification plan
[ ] Check legal notification requirements for individuals, regulators, or third parties.
[ ] Confirm notification sequencing (e.g., regulator before individual).
[ ] Determine internal vs. third-party logistics for printing, mailing, or support.
[ ] Consider offering credit monitoring or identity theft protection.
[ ] Create a legal compliance timeline for deadlines.
Execute the notification plan
[ ] Track individuals notified:
[ ] Names, addresses, contact info, affected data elements, and status.
[ ] Choose notification method (mail, email, public posting).
[ ] Prepare template letters based on legal needs (e.g., minors, deceased).
[ ] Notify credit agencies and regulators with tailored letters.
[ ] Use substitute notices where individuals can't be reached, in line with law.
Post-notification
[ ] Review access and security controls used during the breach.
[ ] Identify policy gaps or weaknesses exposed during the incident.
[ ] Update the security program based on breach analysis.
[ ] Conduct risk assessments using frameworks like NIST to identify vulnerabilities.
Benefits of using a responding to a data breach checklist
A responding to a data breach checklist offers multiple advantages, ensuring that your organization manages the breach effectively and complies with legal requirements. Here’s how it helps:
- Ensure compliance with legal obligations: The checklist helps you stay aligned with federal, state, and industry-specific laws, reducing the risk of penalties or legal actions. It guides you through the necessary steps to meet notification requirements, regulatory disclosures, and data protection laws like GDPR or HIPAA.
- Streamline your response process: A structured checklist helps you act quickly and systematically in the event of a data breach, minimizing chaos and ensuring that all critical steps are covered. This not only reduces the impact of the breach but also helps limit further damage to your systems and reputation.
- Minimize business disruption: By following the checklist, you can ensure that your response team contains the breach and mitigates its effects without major interruptions to business operations. The clear instructions make it easier to focus on containment and remediation.
- Protect your reputation: The checklist helps you manage communication with affected parties, media, regulators, and law enforcement in a timely and professional manner. This transparency and quick response can help preserve trust with customers, partners, and stakeholders.
- Prepare for future incidents: Documenting your response allows you to learn from each breach. The checklist provides a solid foundation for post-breach analysis, helping you strengthen your cybersecurity program and be better prepared for future incidents.
Frequently asked questions (FAQs)
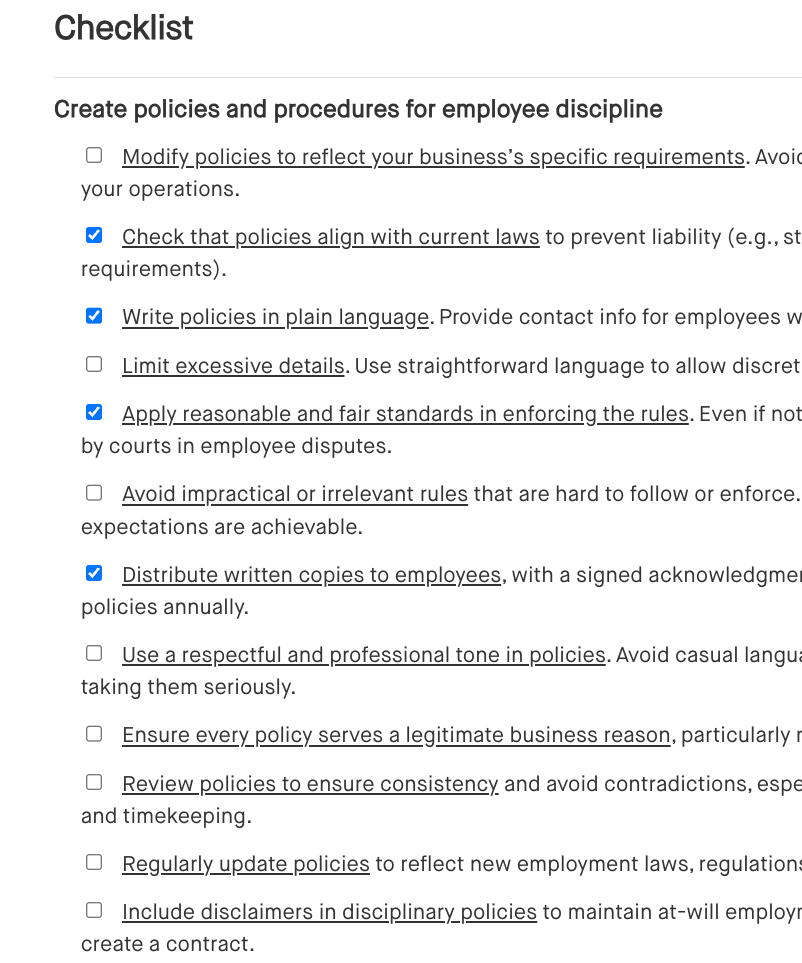
Outlines steps to address employee behavior or performance issues, ensuring fair, consistent, and documented disciplinary actions.
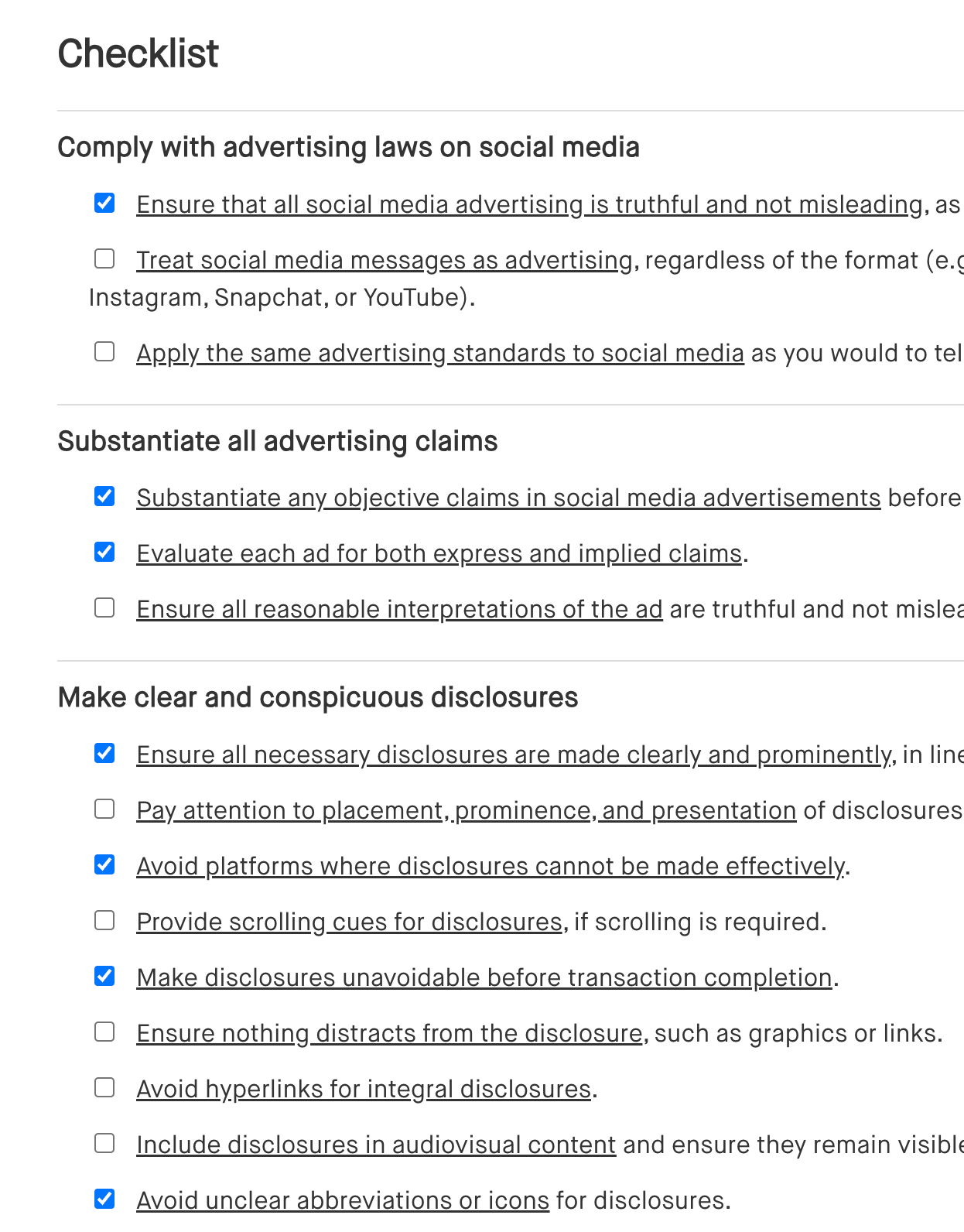
Outlines the essential steps for planning and executing advertising and promotions on social media, promoting compliance, effective targeting, and tracking of results.

Outlines the key factors to consider when selecting a new vendor, ensuring a thorough evaluation of their capabilities, reliability, and alignment with your business needs.