Bring your own device to work policy (Oklahoma): Free template
Got contracts to review? While you're here for policies, let Cobrief make contract review effortless—start your free review now.
Customize this template for free
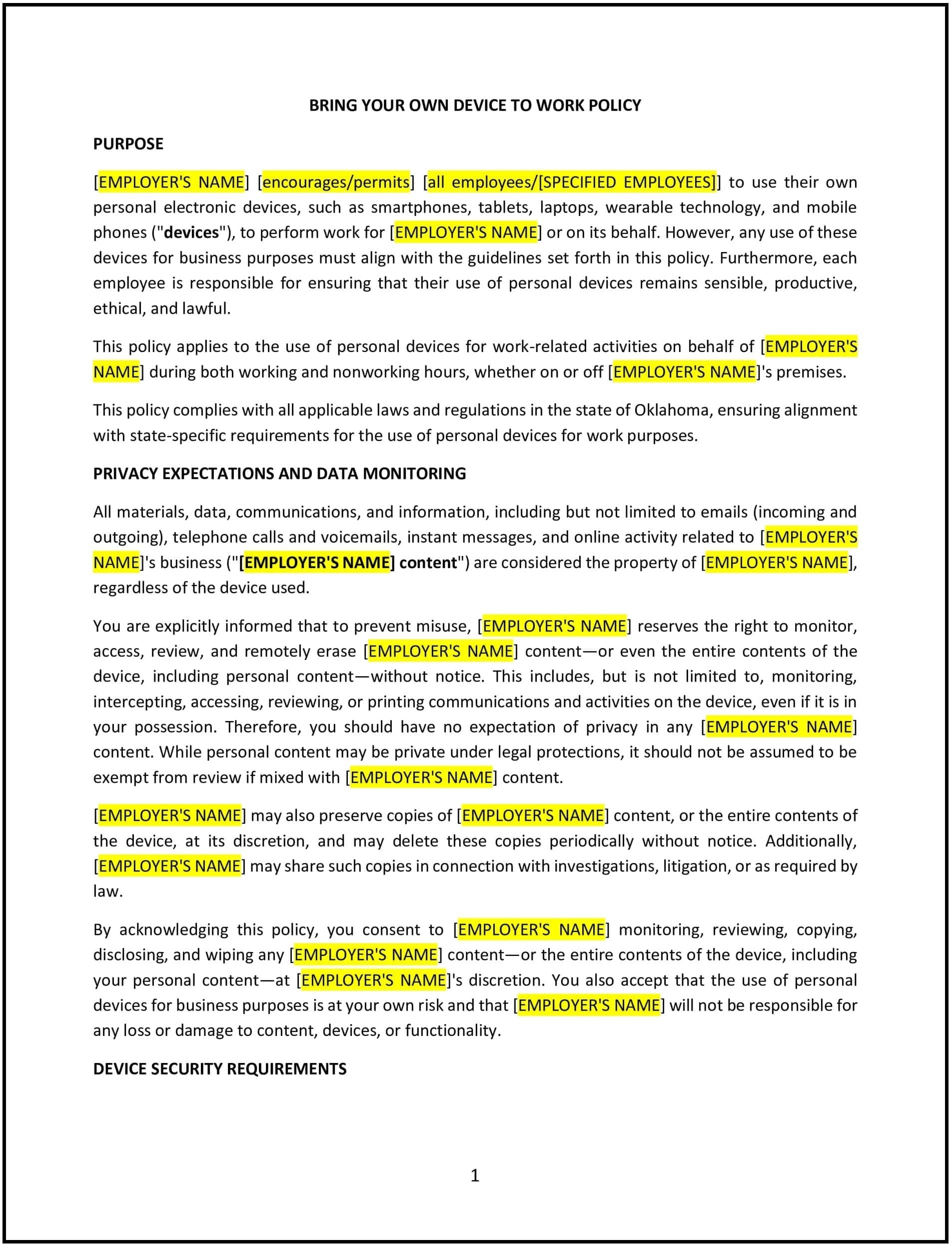
Bring your own device to work policy (Oklahoma)
This bring your own device (BYOD) policy is designed to help Oklahoma businesses establish clear guidelines for employees using personal devices for work purposes. The policy outlines security measures, acceptable use, and data protection requirements to minimize risks while maintaining operational efficiency.
By implementing this policy, businesses can balance flexibility with security, ensuring that employee-owned devices do not pose a threat to company systems or sensitive information.
How to use this bring your own device to work policy (Oklahoma)
- Define permitted devices: Specify which personal devices, such as smartphones, tablets, and laptops, can be used for work.
- Establish security requirements: Require employees to use strong passwords, enable encryption, and keep software updated.
- Outline acceptable use: Clarify how personal devices may be used for work, including restrictions on unauthorized applications or data storage.
- Address company data protection: Ensure that employees using personal devices follow protocols for accessing, storing, and transmitting sensitive business information.
- Implement monitoring and compliance: Detail how the company will oversee compliance, including potential audits or security checks.
- Specify reimbursement policies: Clarify whether the business will provide reimbursements for device costs, data plans, or security software.
- Review regularly: Periodically assess the policy to align with evolving cybersecurity threats and Oklahoma-specific business needs.
Benefits of using this bring your own device to work policy (Oklahoma)
Implementing this policy provides several advantages for Oklahoma businesses:
- Enhances flexibility: Allows employees to work efficiently using their own devices.
- Reduces costs: Minimizes business expenses on company-issued devices while maintaining security.
- Strengthens data protection: Enforces security protocols to safeguard company information on personal devices.
- Improves compliance: Ensures that all employees using personal devices adhere to company IT and cybersecurity standards.
- Reflects Oklahoma-specific considerations: Adapts to local business practices and regulatory expectations.
Tips for using this bring your own device to work policy (Oklahoma)
- Communicate security protocols: Educate employees on cybersecurity best practices when using personal devices for work.
- Enforce access controls: Implement multi-factor authentication (MFA) and other security measures for accessing company systems.
- Monitor compliance: Use IT tools to track device access and detect potential security risks.
- Provide IT support: Offer guidance on setting up secure configurations and troubleshooting device issues.
- Update policies regularly: Review and adjust the policy based on technological advancements and emerging security threats.