Information security policy (Arkansas): Free template
Got contracts to review? While you're here for policies, let Cobrief make contract review effortless—start your free review now.
Customize this template for free
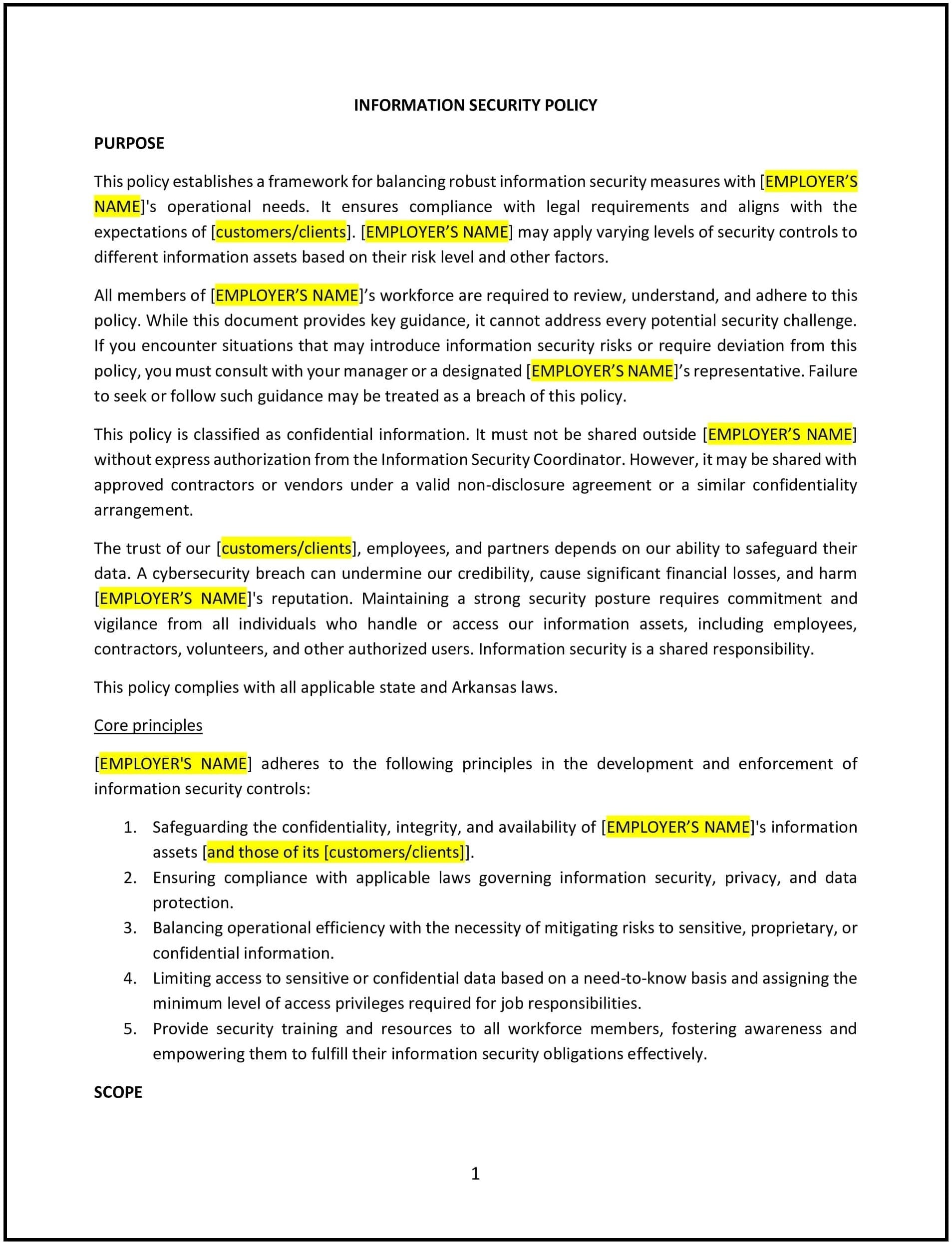
Information security policy (Arkansas)
In Arkansas, an information security policy provides businesses with a framework for protecting sensitive data, safeguarding systems, and ensuring compliance with data protection regulations. This policy outlines the responsibilities of employees, security protocols, and procedures for managing potential threats.
By implementing this policy, Arkansas businesses can mitigate cybersecurity risks, enhance trust with customers and partners, and support compliance with applicable state and federal regulations, such as the Gramm-Leach-Bliley Act (GLBA) or Arkansas’s data breach notification laws.
How to use this information security policy (Arkansas)
- Define security protocols: Clearly outline procedures for safeguarding sensitive data, including encryption, access controls, and secure storage.
- Assign responsibilities: Specify the roles of employees and IT personnel in maintaining information security and responding to incidents.
- Establish data classification: Identify different types of data (e.g., public, confidential, sensitive) and the security measures required for each category.
- Develop incident response procedures: Provide guidelines for detecting, reporting, and managing security breaches to minimize impact.
- Provide training: Educate employees on best practices for information security, such as recognizing phishing attempts and using strong passwords.
Benefits of using this information security policy (Arkansas)
This policy offers several advantages for Arkansas businesses:
- Reduces cybersecurity risks: Protects systems and data from unauthorized access, theft, or breaches.
- Enhances trust: Demonstrates the business’s commitment to safeguarding sensitive information, building trust with customers and stakeholders.
- Supports compliance: Aligns with Arkansas-specific regulations and federal laws to ensure legal and regulatory adherence.
- Improves response readiness: Establishes clear procedures for managing security incidents, minimizing potential damage and downtime.
- Promotes accountability: Clarifies employee and management roles in maintaining a secure workplace.
Tips for using this information security policy (Arkansas)
- Address Arkansas-specific considerations: Incorporate state laws governing data protection and breach notifications into the policy.
- Implement monitoring tools: Use software solutions to detect and respond to potential security threats in real-time.
- Conduct regular audits: Periodically review security practices to identify vulnerabilities and ensure compliance with the policy.
- Update regularly: Revise the policy to reflect changes in technology, regulations, or business needs.
- Communicate expectations: Ensure all employees understand their role in maintaining information security and complying with the policy.