Information security policy (California): Free template
Got contracts to review? While you're here for policies, let Cobrief make contract review effortless—start your free review now.
Customize this template for free
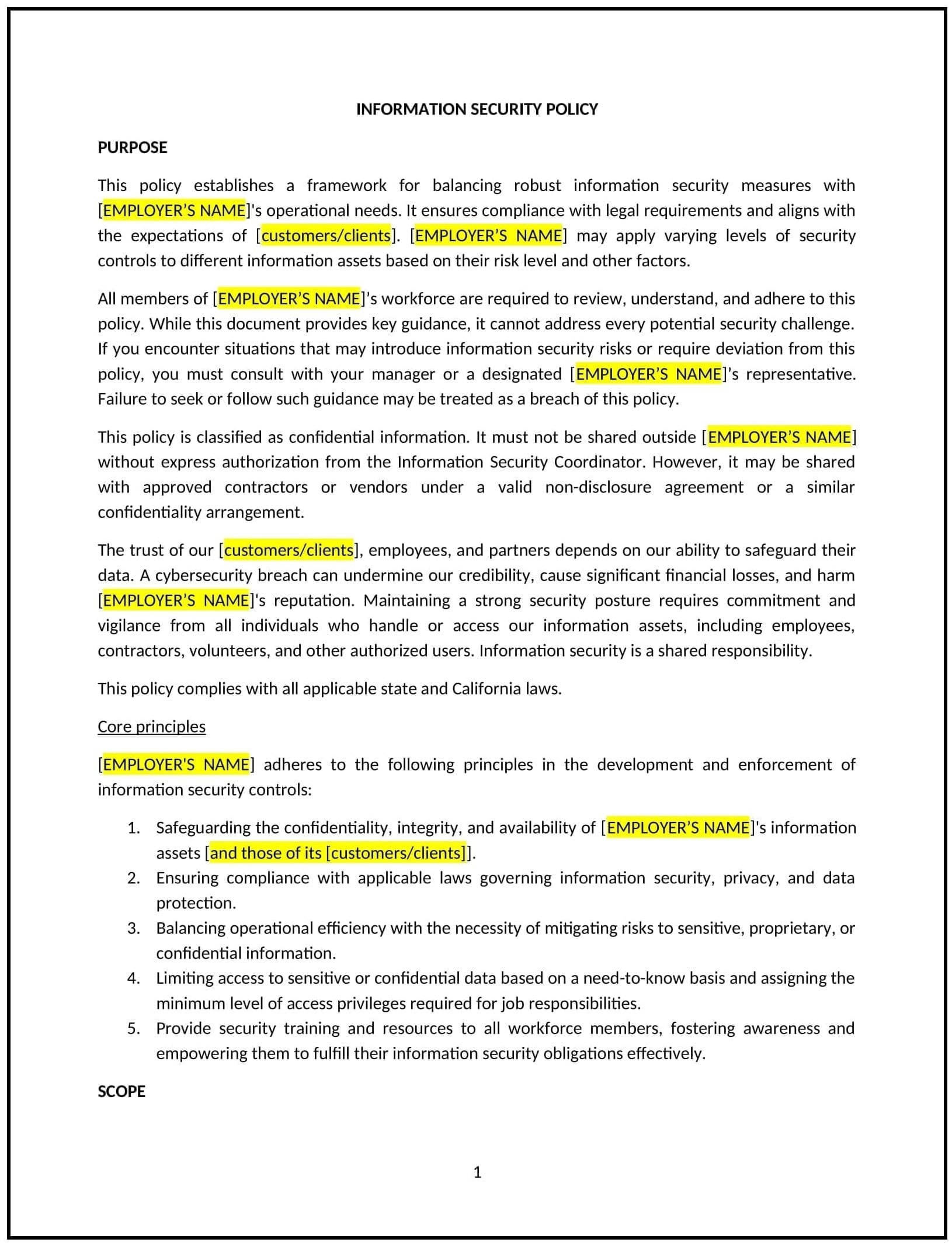
Information security policy (California)
In California, an information security policy provides businesses with guidelines to protect sensitive data, prevent unauthorized access, and comply with state regulations, such as the California Consumer Privacy Act (CCPA) and the California Privacy Rights Act (CPRA). This policy outlines the business’s approach to safeguarding digital and physical information assets.
This policy covers procedures for managing data access, implementing security controls, and responding to security incidents. By implementing this policy, California businesses can reduce risks, protect their reputation, and foster trust among customers and stakeholders.
How to use this information security policy (California)
- Define scope: Specify the types of information covered, including personal data, financial records, and proprietary business information.
- Assign roles and responsibilities: Identify individuals or teams responsible for maintaining and monitoring information security.
- Implement access controls: Establish procedures for granting, revoking, and monitoring access to sensitive information.
- Address incident response: Outline steps for identifying, reporting, and mitigating security breaches or data loss incidents.
- Train employees: Provide regular training on best practices for data security and compliance with California-specific privacy laws.
Benefits of using this information security policy (California)
This policy offers several advantages for California businesses:
- Supports compliance: Reflects California privacy laws, such as CCPA and CPRA, ensuring lawful handling of sensitive data.
- Protects assets: Safeguards digital and physical information from breaches, theft, or loss.
- Reduces risks: Minimizes potential legal and financial consequences of data breaches or non-compliance.
- Enhances trust: Demonstrates the business’s commitment to protecting customer and stakeholder information.
- Promotes accountability: Establishes clear responsibilities for information security across the organization.
Tips for using this information security policy (California)
- Reflect California-specific laws: Address requirements under CCPA, CPRA, and other state regulations governing data privacy and security.
- Use secure technologies: Implement encryption, firewalls, and other advanced security measures to protect information assets.
- Monitor access: Regularly review and update access controls to ensure they align with current roles and responsibilities.
- Conduct audits: Periodically assess the effectiveness of security measures and identify areas for improvement.
- Review regularly: Update the policy to reflect changes in California laws, technology, or business operations.