Information security policy (Nebraska): Free template
Got contracts to review? While you're here for policies, let Cobrief make contract review effortless—start your free review now.
Customize this template for free
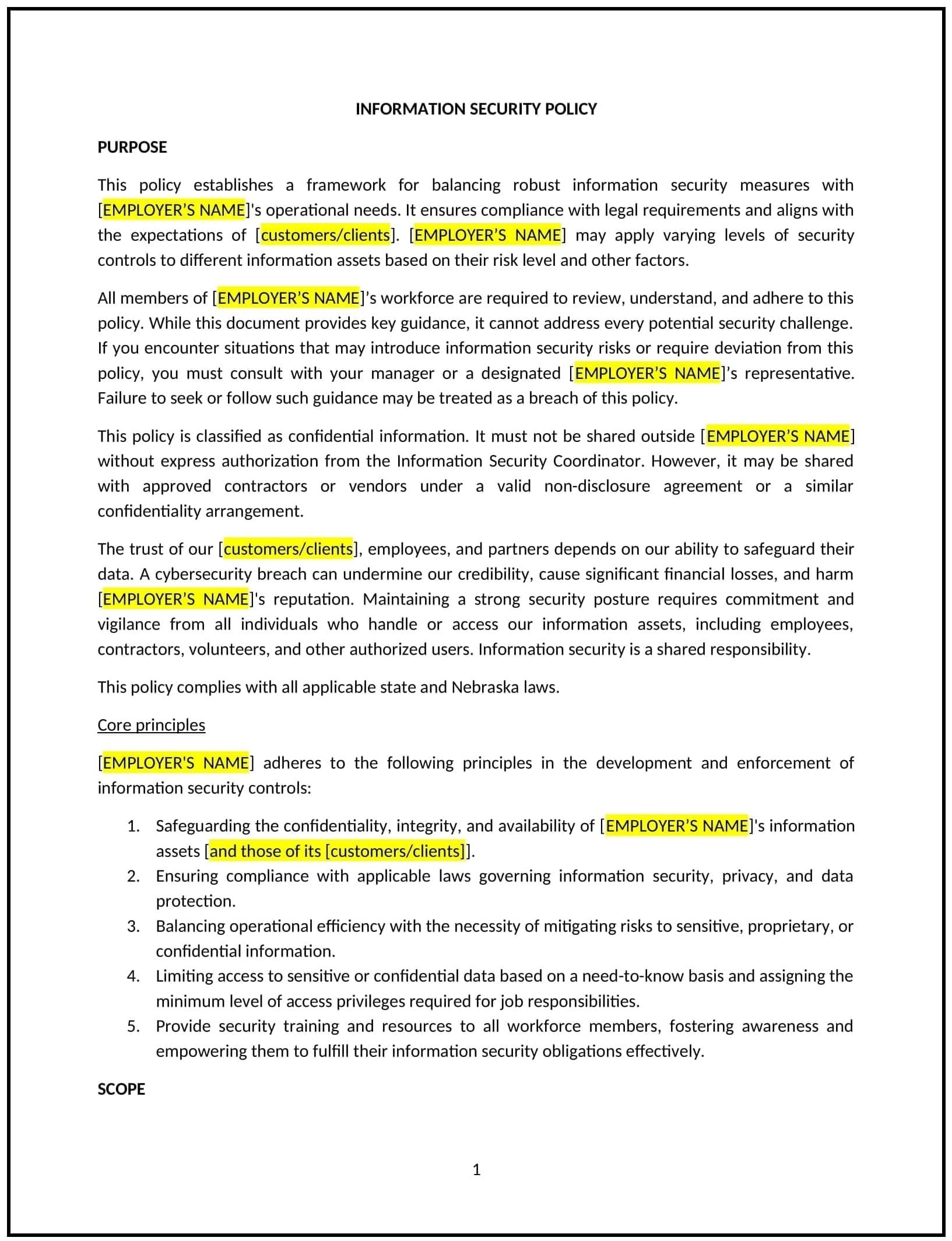
Information security policy (Nebraska)
An information security policy helps Nebraska businesses protect sensitive and confidential data from unauthorized access, use, disclosure, alteration, and destruction. This policy outlines the practices and procedures the business will follow to safeguard data, including personal, financial, and proprietary information. It is designed to protect both the company and its clients from data breaches, cyberattacks, and other security threats, while maintaining the confidentiality, integrity, and availability of information.
By adopting this policy, businesses in Nebraska can mitigate the risks of data loss, cyberattacks, and regulatory violations, and create a secure environment for handling and storing sensitive information.
How to use this information security policy (Nebraska)
- Define information security scope: Clearly specify the types of information that are covered by the policy, including personal data, financial information, intellectual property, customer data, and any other sensitive or confidential business data.
- Assign responsibility for information security: Designate individuals or teams responsible for overseeing information security, such as a Chief Information Security Officer (CISO), IT department, or security team. Define the roles and responsibilities for these individuals in maintaining security and responding to incidents.
- Identify and manage risks: Conduct regular risk assessments to identify potential security threats, vulnerabilities, and risks to the business’s information assets. Outline how these risks will be mitigated through preventive measures, including encryption, firewalls, and access controls.
- Establish data protection measures: Specify the methods used to protect sensitive information, including encryption, secure storage, secure transmission methods (e.g., using HTTPS), and multi-factor authentication (MFA) for accessing sensitive systems.
- Implement access controls: Establish strict access controls that limit access to sensitive information based on the role and need-to-know basis. Employees should only have access to the data required to perform their job functions.
- Monitor and audit information systems: Implement monitoring systems to detect unauthorized access or suspicious activity in real time. Regularly audit systems and data access logs to ensure compliance with the policy and identify potential breaches or weaknesses.
- Develop incident response procedures: Outline the steps to take if an information security breach occurs, including identifying the breach, containing the damage, notifying affected parties, and reporting the incident to relevant authorities as required by law.
- Provide training and awareness: Offer regular training to employees on information security best practices, including how to handle sensitive data, recognize phishing attempts, and protect against cyber threats. Promote a culture of security awareness within the company.
- Ensure third-party security: Require vendors, contractors, and other third parties to comply with the company’s information security policies and perform security assessments to ensure that they meet the necessary security standards.
- Review and update: Periodically review and update the information security policy to reflect emerging threats, technological changes, and regulatory updates. Ensure the policy remains relevant and effective in protecting company data.
Benefits of using this information security policy (Nebraska)
This policy provides several benefits for Nebraska businesses:
- Protects sensitive data: A strong information security policy helps safeguard personal, financial, and proprietary information from unauthorized access or cyberattacks, reducing the risk of data breaches.
- Increases customer trust: Businesses that prioritize information security demonstrate a commitment to protecting customer data, which builds trust and strengthens customer relationships.
- Minimizes legal risks: By adhering to data protection regulations and following best practices, businesses can avoid legal penalties and reputational damage resulting from data breaches or non-compliance with industry standards.
- Improves operational efficiency: With clear guidelines for securing data, businesses can streamline processes and ensure that sensitive information is handled securely, reducing inefficiencies and operational risks.
- Enhances reputation: A company with robust information security practices is viewed as a responsible and trustworthy entity, which can attract customers, partners, and investors who prioritize security.
Tips for using this information security policy (Nebraska)
- Communicate the policy clearly: Ensure all employees are aware of the information security policy and understand their role in safeguarding company data. Include the policy in employee handbooks, onboarding, and regular training sessions.
- Provide ongoing training: Regularly train employees on information security best practices, such as recognizing phishing emails, handling sensitive data, and using secure passwords. Offer refresher courses to keep security practices up-to-date.
- Implement technical safeguards: Invest in firewalls, encryption, and intrusion detection systems to protect company data. Ensure that employees use strong passwords and multi-factor authentication (MFA) to access sensitive information.
- Regularly review security measures: Conduct regular security audits and risk assessments to identify any vulnerabilities or gaps in the company’s security measures. Address any weaknesses promptly to reduce the risk of security breaches.
- Engage third-party experts: Consider working with third-party security experts to conduct audits, penetration testing, and vulnerability assessments to ensure that your business is meeting industry standards and addressing potential threats.
- Monitor and respond to incidents: Set up a monitoring system that detects unauthorized access or suspicious activities. Have a clear, well-documented response plan in place in case of a data breach or security incident.