Information security policy (Wyoming): Free template
Got contracts to review? While you're here for policies, let Cobrief make contract review effortless—start your free review now.
Customize this template for free
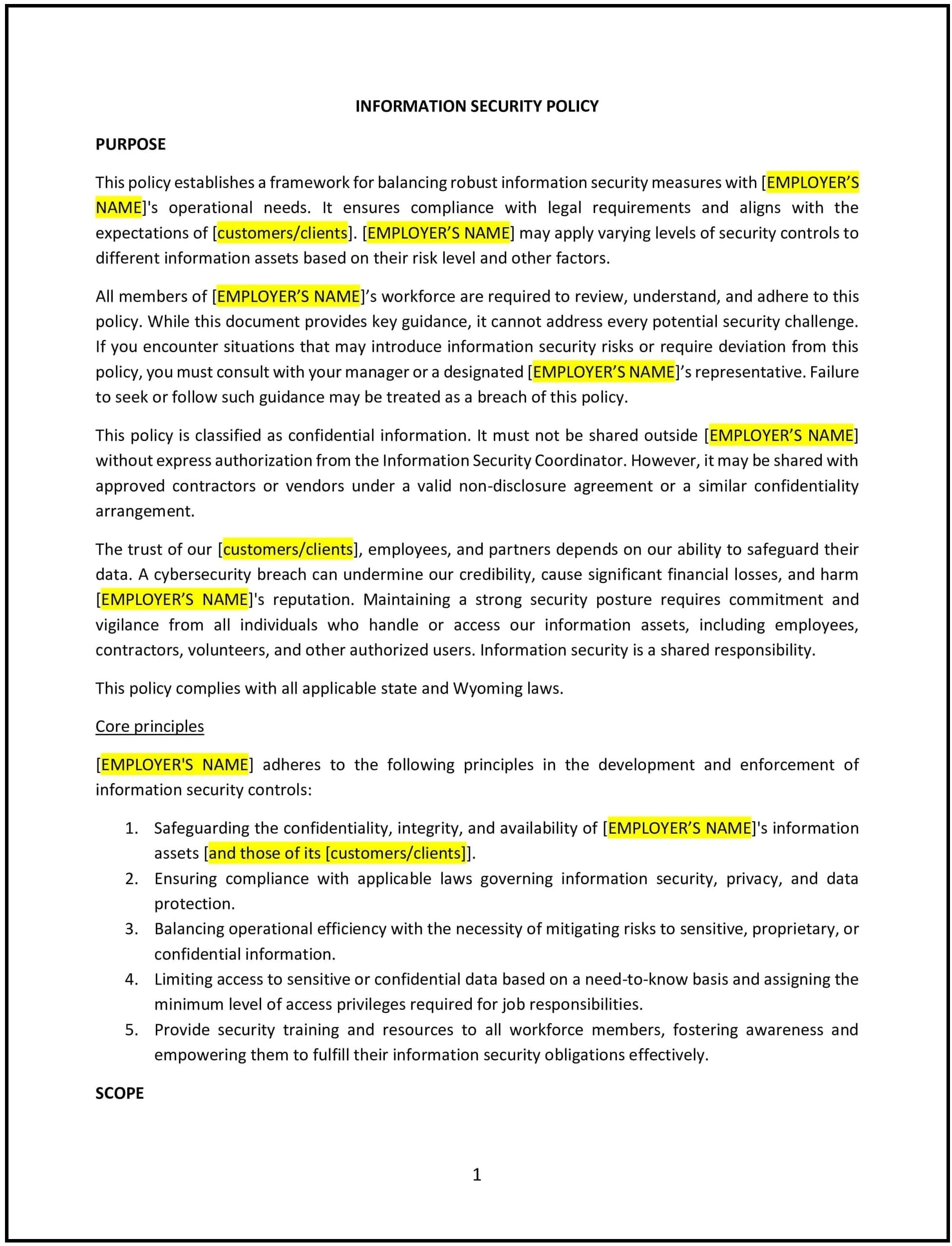
Information security policy (Wyoming)
In Wyoming, an information security policy helps businesses safeguard sensitive data, protect against cyber threats, and promote compliance with state and federal regulations. This policy is critical for organizations handling confidential information, such as customer data, intellectual property, and financial records.
This policy outlines the principles, responsibilities, and procedures for protecting information assets, ensuring a secure and resilient approach to data management.
How to use this information security policy (Wyoming)
- Define scope and objectives: Clearly outline the scope of the policy, including the types of information assets covered, and specify the organization’s commitment to maintaining security.
- Assign roles and responsibilities: Identify key personnel responsible for implementing and maintaining information security, such as IT staff, managers, and employees.
- Implement security measures: Detail the technical and organizational measures to protect information, such as firewalls, encryption, access controls, and secure backup systems.
- Establish incident response procedures: Include steps for identifying, reporting, and responding to security breaches, ensuring swift action to minimize impact.
- Support compliance: Align the policy with Wyoming laws, industry standards, and federal regulations, such as HIPAA or PCI DSS, to support legal and ethical data handling.
Benefits of using an information security policy (Wyoming)
A robust information security policy provides several advantages for Wyoming businesses:
- Protects sensitive data: Safeguards customer, employee, and business information from unauthorized access or breaches.
- Supports compliance: Ensures alignment with legal and regulatory requirements, reducing the risk of fines or penalties.
- Reduces risks: Minimizes vulnerabilities to cyber threats, such as hacking, phishing, or ransomware attacks.
- Enhances trust: Demonstrates a commitment to security, building trust with customers, partners, and stakeholders.
- Adapts to local needs: Addresses Wyoming’s unique business environment and technology challenges.
Tips for using an information security policy (Wyoming)
- Provide training: Educate employees on best practices for data security, such as recognizing phishing attempts and using strong passwords.
- Monitor and audit systems: Regularly review security measures to identify vulnerabilities and ensure compliance with the policy.
- Use technology: Leverage advanced tools, such as multi-factor authentication and endpoint protection, to strengthen security.
- Engage stakeholders: Collaborate with IT teams, legal advisors, and employees to ensure the policy is practical and effective.
- Review periodically: Update the policy to reflect changes in technology, threats, or regulatory requirements.