IT and electronics communications policy (Oklahoma): Free template
Got contracts to review? While you're here for policies, let Cobrief make contract review effortless—start your free review now.
Customize this template for free
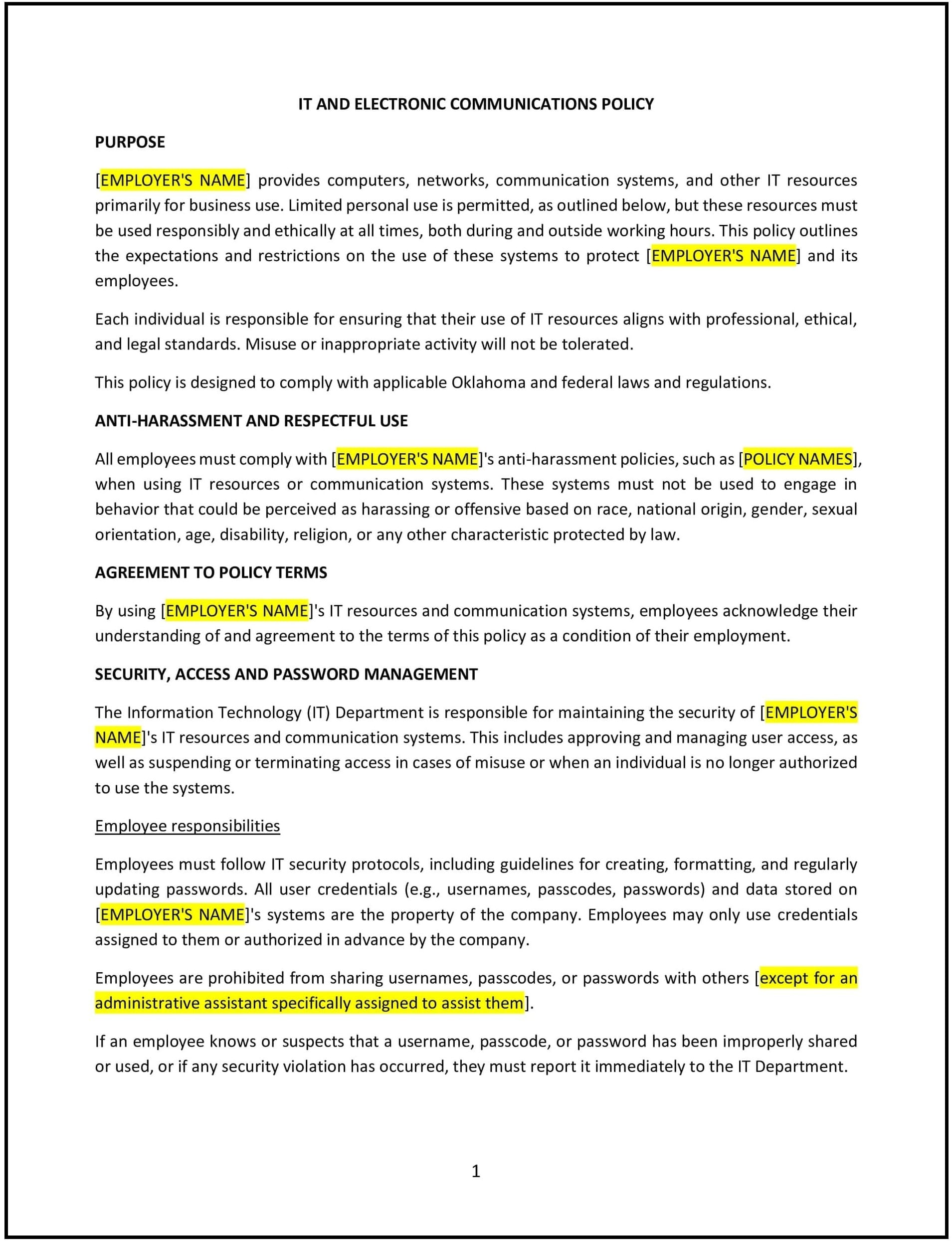
IT and electronics communications policy (Oklahoma)
This IT and electronics communications policy is designed to help Oklahoma businesses establish guidelines for the proper use of company technology, electronic communications, and digital resources. The policy outlines acceptable use, security measures, and employee responsibilities to protect company data and ensure efficient use of IT resources.
By implementing this policy, businesses can minimize cybersecurity risks, prevent misuse of company systems, and promote responsible digital communication.
How to use this IT and electronics communications policy (Oklahoma)
- Define acceptable use: Specify permitted activities for company-owned devices, networks, and communication tools.
- Set email and messaging guidelines: Outline appropriate use of business emails, instant messaging, and collaboration platforms.
- Establish data security protocols: Require encryption, password protection, and secure access to sensitive information.
- Prohibit unauthorized software and downloads: Restrict installation of unapproved programs to prevent security vulnerabilities.
- Address personal device use: Set rules for accessing company systems through personal laptops, phones, or tablets.
- Implement monitoring and compliance measures: Inform employees that IT activity may be monitored to ensure security and prevent misuse.
- Review regularly: Update the policy periodically to align with evolving cybersecurity threats and technological advancements.
Benefits of using this IT and electronics communications policy (Oklahoma)
Implementing this policy provides several advantages for Oklahoma businesses:
- Enhances cybersecurity: Reduces risks of data breaches, phishing attacks, and unauthorized access.
- Improves workplace productivity: Establishes clear guidelines for the use of company IT resources.
- Supports compliance with data protection laws: Helps businesses align with Oklahoma and federal IT regulations.
- Protects company reputation: Ensures professional and secure communication practices.
- Reflects Oklahoma-specific business considerations: Addresses regional cybersecurity concerns and workplace technology trends.
Tips for using this IT and electronics communications policy (Oklahoma)
- Train employees on cybersecurity awareness: Provide guidance on phishing prevention, password management, and safe browsing habits.
- Enforce strong access controls: Require multi-factor authentication (MFA) and role-based permissions.
- Monitor IT system usage: Regularly audit employee access to sensitive company data.
- Maintain data backup procedures: Ensure business-critical information is backed up securely.
- Adjust policies as needed: Update IT security protocols based on emerging threats and regulatory changes.