Now do IT and electronics communications policy (Connecticut): Free template
Got contracts to review? While you're here for policies, let Cobrief make contract review effortless—start your free review now.
Customize this template for free
IT and electronics communications policy (Connecticut)
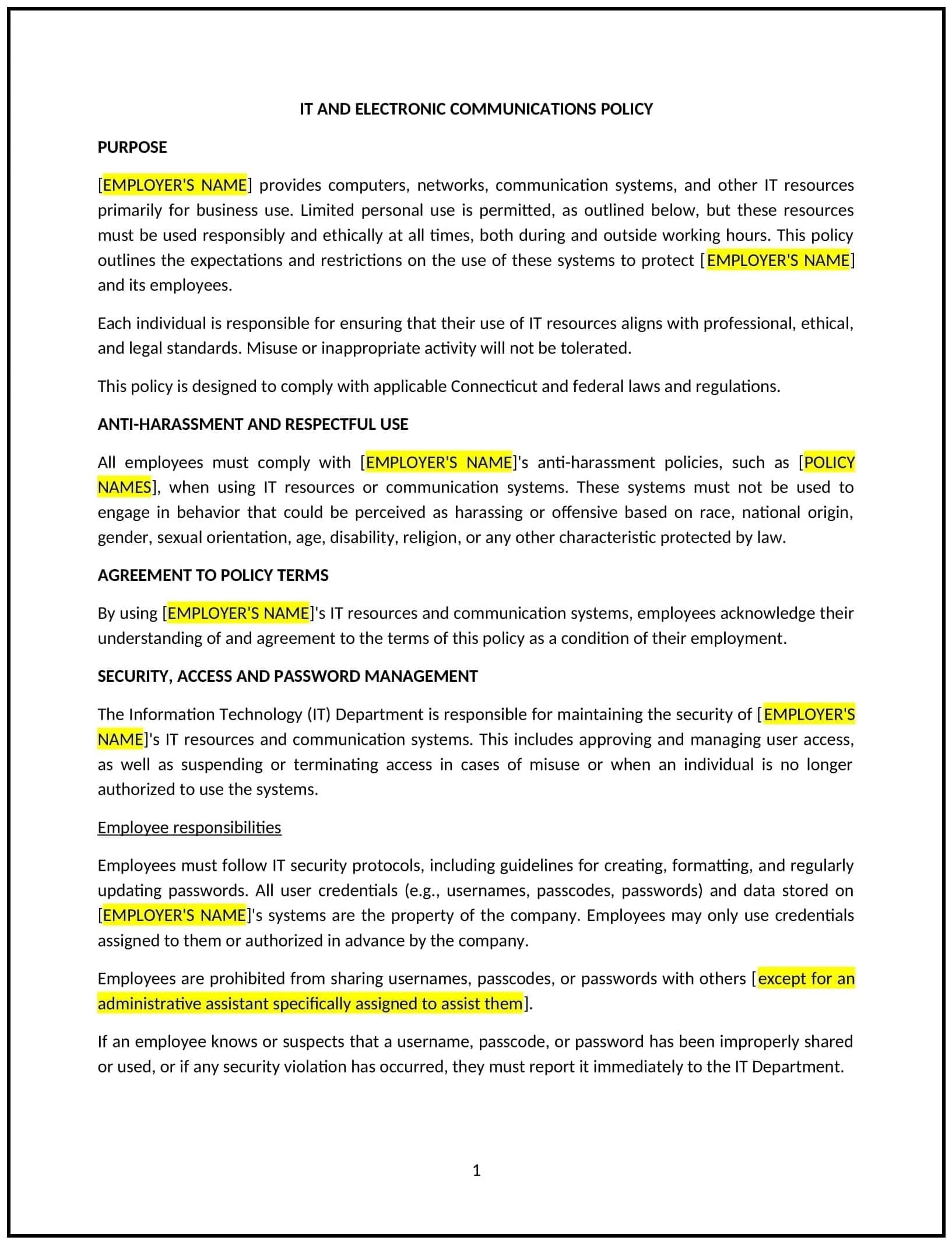
An IT and electronics communications policy helps Connecticut businesses set guidelines for the appropriate use of company-provided electronic devices, networks, and communications systems. This policy outlines acceptable use, security protocols, and the responsibilities of employees when using company technology for work-related communications, including email, instant messaging, and internet access.
By implementing this policy, businesses can reduce the risk of data breaches, maintain productivity, and ensure that company resources are used responsibly and in compliance with applicable laws.
How to use this IT and electronics communications policy (Connecticut)
- Define acceptable use: Clearly explain what constitutes acceptable use of company-provided technology and communications tools, including email, internet access, and personal device usage during work hours.
- Set security protocols: Outline the company’s security requirements, such as the use of passwords, encryption, and secure networks, to protect company data and prevent unauthorized access.
- Monitor communications: Specify the company’s right to monitor communications on company-provided devices, including emails and internet browsing, while respecting employees' privacy rights in accordance with applicable laws.
- Provide guidelines for remote work: Establish rules for employees working remotely, including how to securely access company systems and maintain confidentiality when using personal devices.
- Address prohibited activities: List activities that are not allowed, such as accessing inappropriate websites, using company resources for personal gain, or engaging in harassment or illegal activities via electronic communications.
- Ensure compliance with laws: Make sure the policy complies with applicable Connecticut state laws, federal regulations (e.g., the Computer Fraud and Abuse Act), and industry best practices related to data security, privacy, and electronic communications.
Benefits of using this IT and electronics communications policy (Connecticut)
This policy offers several benefits for Connecticut businesses:
- Protects company data: By outlining security protocols, the policy helps protect sensitive business data, preventing unauthorized access and reducing the risk of data breaches.
- Increases productivity: Clear guidelines on acceptable use help employees focus on work-related tasks while minimizing distractions from personal internet use or unapproved applications.
- Complies with legal requirements: Ensures that the business adheres to privacy and data protection laws, avoiding legal risks associated with the misuse of electronic communications or devices.
- Prevents misuse of resources: Helps reduce misuse of company resources for personal gain or inappropriate activities, maintaining professionalism and efficiency in the workplace.
- Promotes a secure remote work environment: Provides guidelines for remote workers on how to securely access company systems and maintain data confidentiality, supporting business continuity and employee productivity.
Tips for using this IT and electronics communications policy (Connecticut)
- Communicate the policy clearly: Ensure that all employees understand the rules regarding the use of company-provided devices, email, and internet access, as well as the importance of maintaining security.
- Implement regular training: Provide training to employees on best practices for using technology securely and responsibly, including how to identify phishing attempts, protect passwords, and handle sensitive information.
- Monitor usage appropriately: Establish a clear process for monitoring electronic communications to ensure compliance with the policy while respecting employee privacy rights.
- Provide secure remote access: Ensure that employees working remotely have secure access to company systems and follow the same security protocols as if they were in the office.
- Review periodically: Update the policy regularly to address emerging security threats, changes in laws, or business needs, ensuring it remains relevant and effective.