Start a new document with this content. Open the editor to build from scratch — paste in what you need and keep writing.
Obtaining cyber insurance checklist
Cyber insurance is crucial in today’s digital world to help businesses handle the financial fallout from cyber attacks. From data breaches to phishing scams, cyber threats can lead to major disruptions and costs. This checklist will walk you through the steps to assess, apply for, and manage cyber insurance that fits your business.
Whether you’re safeguarding your own systems or covering potential liabilities to others, having the right coverage in place can be a game-changer when dealing with cyber risks.
How to use this cyber insurance checklist
- Follow the steps in order: Start by understanding the cyber insurance market, your coverage needs, and the types of incidents that trigger coverage. Then move on to evaluating your risks, applying for coverage, and reviewing the policy terms.
- Tailor the checklist to your business: Each business has unique risks and coverage requirements. Customize the checklist by considering your specific industry, data handling practices, and cyber threat landscape.
- Work with key stakeholders: Involve key departments such as IT, legal, risk management, and operations to ensure you have a comprehensive view of your company’s cyber risk profile and coverage needs.
- Update regularly: As your business grows or evolves, review and update your cyber insurance policy and this checklist. Cyber threats are constantly changing, and your coverage should keep pace with them.
- Use it for ongoing management: Cyber insurance isn’t just a one-time purchase. Continue to assess your coverage, ensure compliance with the policy conditions, and review your policy language annually to adapt to new risks.
Checklist
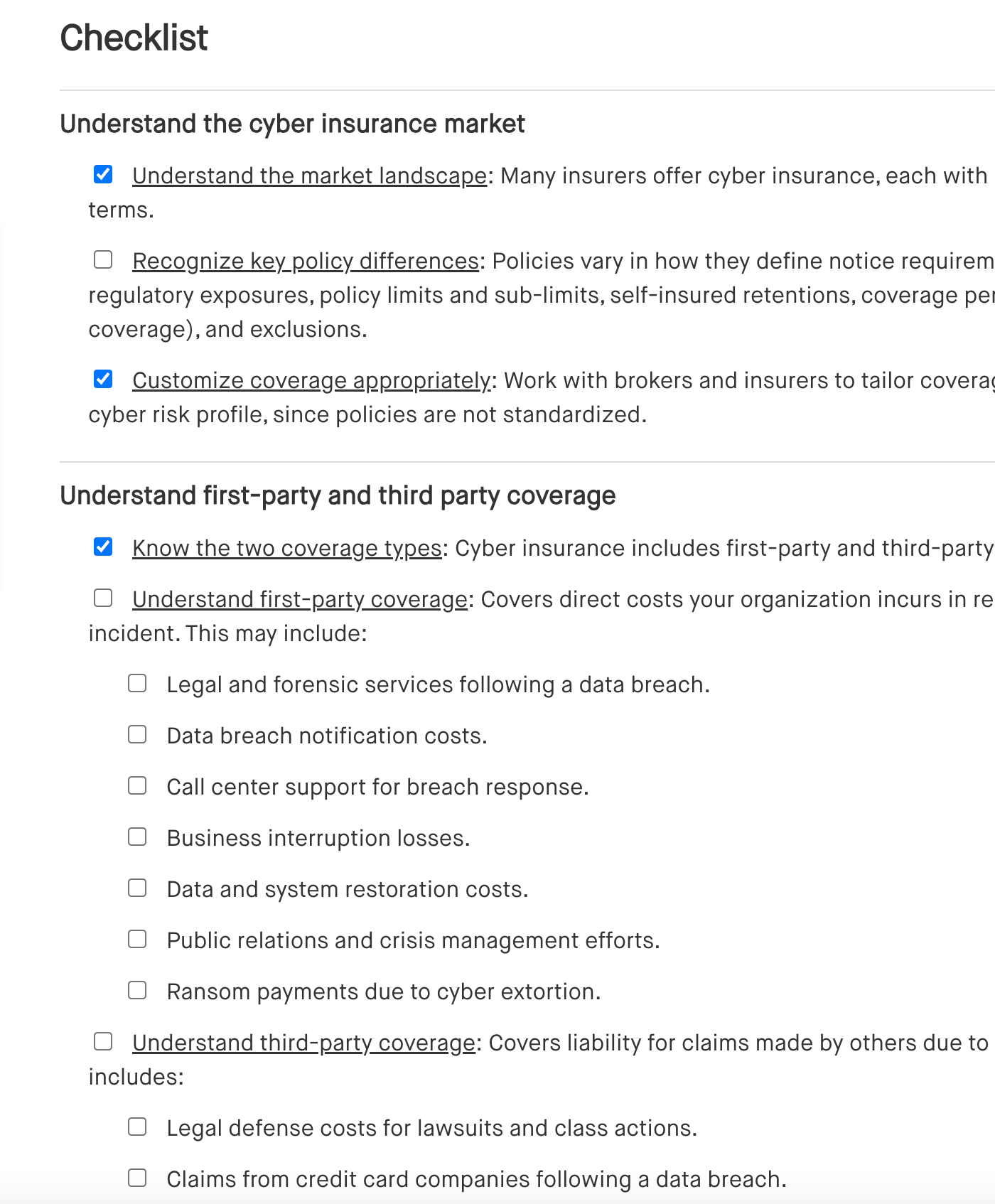
Understand the cyber insurance market
[ ] Understand the market landscape: Many insurers offer cyber insurance, each with different policy language and terms.
[ ] Recognize key policy differences: Policies vary in how they define notice requirements, coverage scope, regulatory exposures, policy limits and sub-limits, self-insured retentions, coverage periods (including retroactive coverage), and exclusions.
[ ] Customize coverage appropriately: Work with brokers and insurers to tailor coverage that fits your organization’s cyber risk profile, since policies are not standardized.
Understand first-party and third party coverage
[ ] Know the two coverage types: Cyber insurance includes first-party and third-party coverage.
[ ] Understand first-party coverage: Covers direct costs your organization incurs in responding to a covered cyber incident. This may include:
[ ] Legal and forensic services following a data breach.
[ ] Data breach notification costs.
[ ] Call center support for breach response.
[ ] Business interruption losses.
[ ] Data and system restoration costs.
[ ] Public relations and crisis management efforts.
[ ] Ransom payments due to cyber extortion.
[ ] Understand third-party coverage: Covers liability for claims made by others due to a cyber incident. This typically includes:
[ ] Legal defense costs for lawsuits and class actions.
[ ] Claims from credit card companies following a data breach.
[ ] Regulatory investigations and fines.
[ ] Defamation or slander claims from website content.
[ ] Liability for transmitting malware or viruses to others.
Understand claims-made and retroactive coverage
[ ] Know how coverage is triggered: Third-party cyber coverage is typically claims-made, meaning coverage applies if a claim is made during the active policy period.
[ ] Understand coverage triggers: Cyber policies often contain different coverage types with varying triggers, such as:
[ ] Claims-made coverage (triggered when a claim is made).
[ ] Occurrence-based coverage (triggered by the event itself).
[ ] Discovery-based coverage (triggered when an incident is discovered).
[ ] Match coverage to risks: Ensure the policy aligns with your organization’s specific risk profile and needs.
Consider the types of incidents that trigger coverage
[ ] Review the types of incidents that cyber insurance policies may cover, including:
[ ] Data breaches: Covers response and investigation costs, litigation, and regulatory defense and penalties.
[ ] Bricking: Covers repair or replacement costs for hardware that has lost functionality.
[ ] Reputational loss: Covers lost income for a set period (e.g., 30 days) following a security or privacy incident.
[ ] Contingent business interruption: Covers income loss, forensic expenses, and extra costs caused by interruptions of third-party systems.
[ ] Corporate identity theft: Covers losses when a business can’t collect payment due to fraudulent use of its identity.
[ ] Cryptojacking: Covers incidents where malicious actors mine cryptocurrency using your systems.
[ ] Business email compromise: Covers phishing or similar attacks that result in unauthorized transfer of funds.
[ ] Invoice manipulation loss: Covers lost payments from fraudulent invoice or payment instructions after a breach.
[ ] Loss adjustment costs: Covers hiring professionals, like forensic accountants, to assess financial losses.
[ ] Management liability: Covers directors and officers for liabilities related to data privacy and cybersecurity governance.
[ ] Senior executive losses: Covers identity theft and fund theft from executives' personal bank accounts due to company security breaches.
[ ] Telephone and network hacking: Covers losses from hacking, including unauthorized calls or use of company bandwidth.
[ ] Understand that different insurers offer varying types of coverage: Not all businesses may qualify for every type of coverage, some coverages may have sub-limits or require the insurer’s consent before certain actions or expenses. Insurers may match or adjust terms, so work closely with brokers to get the best coverage.
Evaluate regulatory and litigation coverage
[ ] Check if the policy covers claims for regulatory investigations, privacy litigation, fines, and penalties:
[ ] Does it cover specific laws, agencies, or geographic areas?
[ ] Is coverage limited to security events and data breaches, or does it include broader claims related to privacy or data security laws?
[ ] Does it apply to specific types of personal data, or include broader categories like biometric information, browsing history, and geolocation?
[ ] Does it cover claims involving demands for equitable or injunctive relief?
[ ] Are costs for audits and reporting covered?
[ ] Is coverage limited to compensatory damages, or does it also include statutory damages?
[ ] Does the policy exclude coverage for improving privacy or security practices?
[ ] Understand limitations on covered fines and penalties:
[ ] Are fines covered only for specific types of regulatory violations?
[ ] Are intentional or wilful violations excluded from coverage?
[ ] Are punitive fines excluded based on the policy’s governing law?
[ ] Consider state-specific insurance laws: Be aware that some policies only cover fines and penalties if allowed by state law.
[ ] If possible, negotiate where and under which laws coverage disputes will be handled to your advantage.
Recognize common exclusions
[ ] Understand exclusions related to bodily injury and property damage:
[ ] Cyber insurance policies often exclude damages related to bodily injury or property damage.
[ ] Definitions of these terms may vary, and some policies include carve-backs (exceptions to the exclusions).
[ ] Be aware of other common exclusions:
[ ] Claims related to employment practices.
[ ] Claims involving pollution.
[ ] Antitrust violations.
[ ] ERISA violations (Employment Retirement Income Security Act).
[ ] Telephone Consumer Protection Act violations.
[ ] Intentional acts by directors and officers, even if outside their employment scope.
[ ] Unlawful collection of personally identifiable non-public information.
[ ] Negligent cybersecurity practices, such as not installing software patches for known vulnerabilities.
[ ] Incidents involving payment card data unless additional coverage (rider) is purchased.
[ ] Review defined terms carefully: Definitions in the policy may include exclusionary provisions that limit coverage. Be sure to understand how these definitions affect your policy.
Assess cyber risk
[ ] Assemble a cross-functional team: Include stakeholders from IT, information security, privacy/compliance, HR, legal, risk, and key business units like sales, marketing, product, and operations.
[ ] Evaluate your organization’s information security program:
[ ] Determine whether the program is fully developed or in its early stages.
[ ] Assess physical security measures on your premises.
[ ] Identify where data is stored (locally, in the cloud, or with third-party providers).
[ ] Review how and if data is shared with third parties.
[ ] Review past breaches or security events and their associated costs.
[ ] Identify and address gaps in your security program: Remediate any weaknesses found in your information security assessment.
[ ] Be prepared to demonstrate improvements or a plan to address any gaps.
[ ] Consider the nature of data the organization handles:
[ ] Personal data or sensitive personal data (like healthcare or financial information).
[ ] Valuable non-personal data.
[ ] The volume of data the organization holds.
[ ] Data sharing practices with third parties.
[ ] Review your legal responsibilities in the event of a data breach:
[ ] Determine if your organization owns the data or holds it as a vendor.
[ ] Identify the jurisdictions where your business operates or has customers.
[ ] Assess if your organization is in a highly regulated industry.
[ ] Review any indemnification obligations that may arise from data breaches.
[ ] Assess the cost to recreate compromised or breached data for operational continuity or notification requirements.
Assess for cyber coverage
[ ] Gather representatives from legal and risk, privacy and compliance, HR, IT, information security, and business operations to provide necessary information for the cyber insurance application.
[ ] Provide information on the organization’s information security program:
[ ] Include details on the security team structure.
[ ] Specify the percentage of the total IT and operational budget allocated to security.
[ ] Share a copy of the written information security program (WISP).
[ ] Provide any independent security assessments conducted.
[ ] Highlight technical safeguards, such as encryption, firewalls, access controls, and security audits.
[ ] Outline administrative safeguards, including hiring practices and staff training.
[ ] Detail physical security controls like access cards and biometric systems.
[ ] Address third-party controls, such as vendor audits and contracts.
[ ] Include information on data backup processes.
[ ] Be prepared to provide an overview of past data security breaches or incidents.
[ ] Provide relevant company policies and show implementation:
[ ] Internal and external privacy policies.
[ ] Network security and employee training policies.
[ ] Policies governing network, internet, email, and social media use.
[ ] Records management and data destruction policies.
[ ] Incident response plans and procedures.
Review policy language and conditions of coverage
[ ] Analyze policy language:
[ ] Assess how the policy addresses potential data breach scenarios and ensure it provides adequate coverage.
[ ] Review the policy’s definitions to ensure clarity and appropriate coverage.
[ ] Examine exclusions carefully to understand what is not covered.
[ ] Go over all terms and conditions to confirm they align with your organization’s needs.
[ ] Review and negotiate:
[ ] Check the policy’s choice of law provision. If possible, negotiate for the most favorable forum and law for resolving coverage disputes.
[ ] Ensure compliance with the insurer’s expectations, such as implementing encryption standards, conducting security audits, and fixing any identified gaps, and deploying necessary technical, administrative, or other security measures as required by the insurer.
Address post-coverage considerations and periodic reviews
[ ] Be familiar with the notice of claims process for all policies, including:
[ ] Primary policies, including any specific cyber insurance policy.
[ ] Umbrella or excess policies.
[ ] International Commercial General Liability (CGL) or umbrella policies.
[ ] Cancelled or lapsed policies.
[ ] Implement a program to regularly audit and document the organization’s adherence to the conditions of coverage to avoid potential issues with claims.
[ ] When preparing for a merger, acquisition, or similar transaction, review the insurance policy to determine the impact on coverage:
[ ] Confirm if the policy requires the organization to provide advance notice before the transaction.
[ ] Confirm if the insurer requires written consent before the transaction.
[ ] Confirm if the policy requires paying additional premiums.
[ ] Understand that selling or divesting a subsidiary may void that entity's coverage: Some policies may also include provisions triggered by a takeover or acquisition of the named insured.
Frequently asked questions (FAQs)
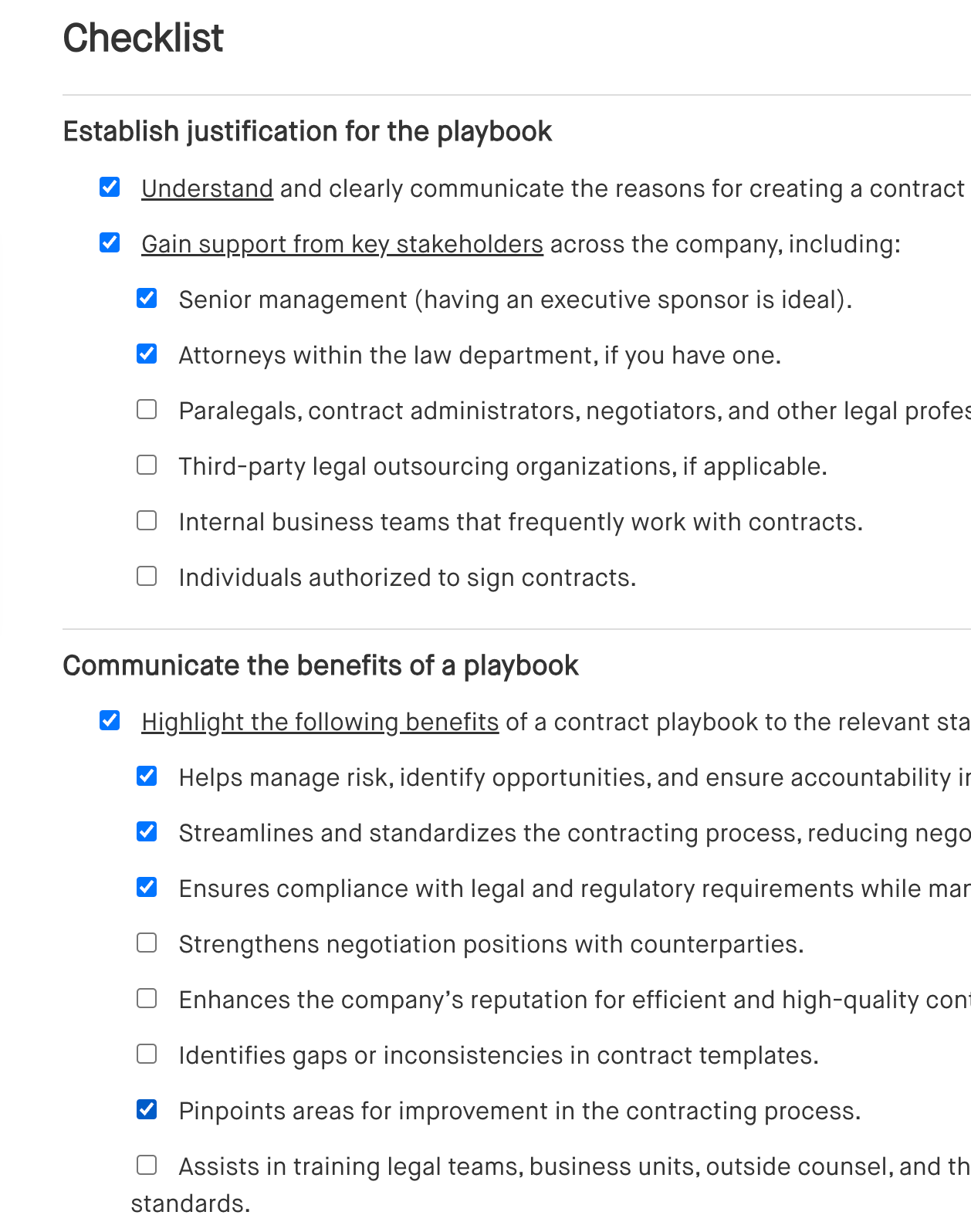
Outlines key elements for creating a contract playbook, including standard clauses, approval workflows, risk management guidelines, and templates for common contract types.
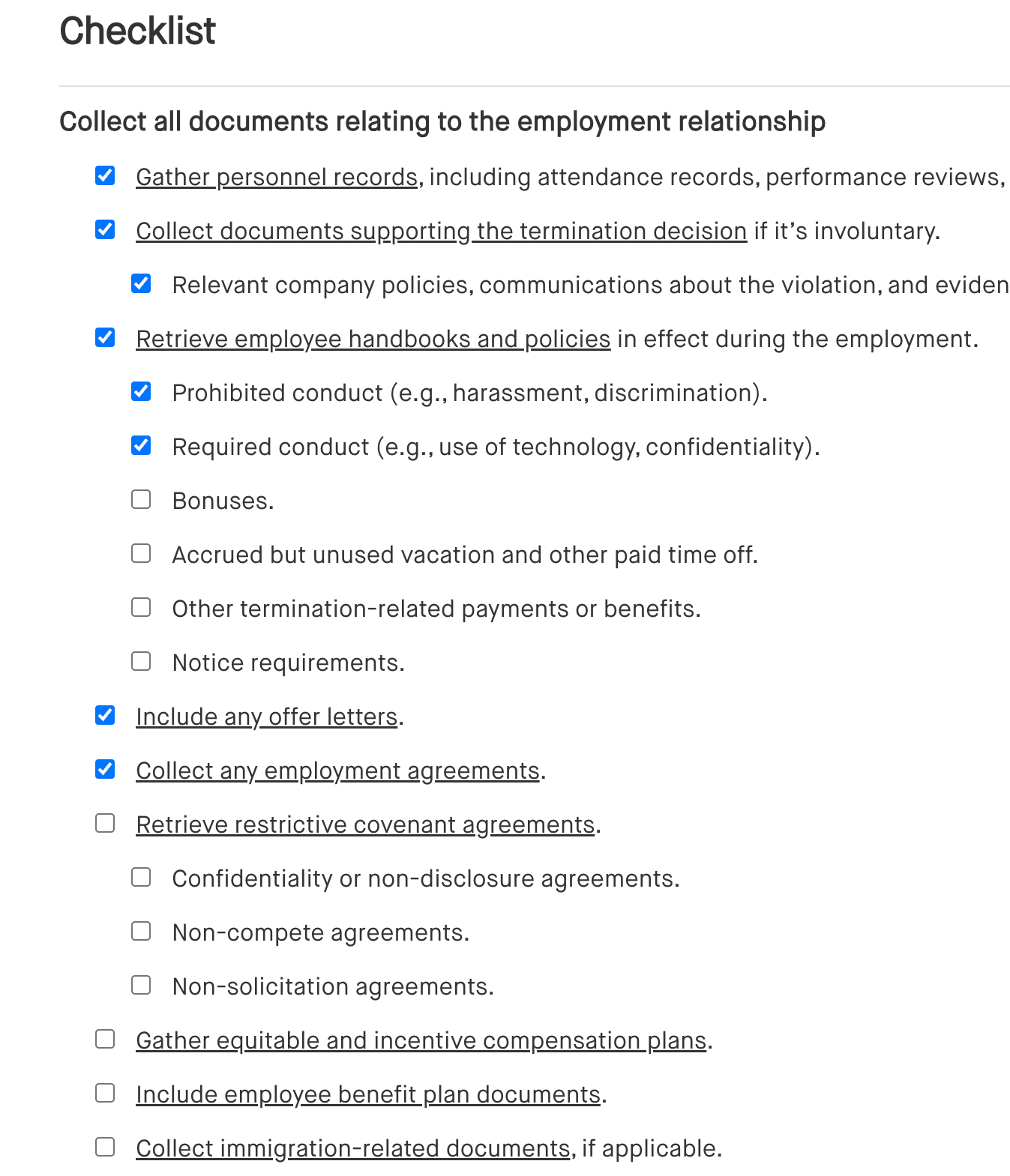
Lists essential steps when handling a departing employee, including exit interviews, return of company property, final paycheck, and updating access permissions.
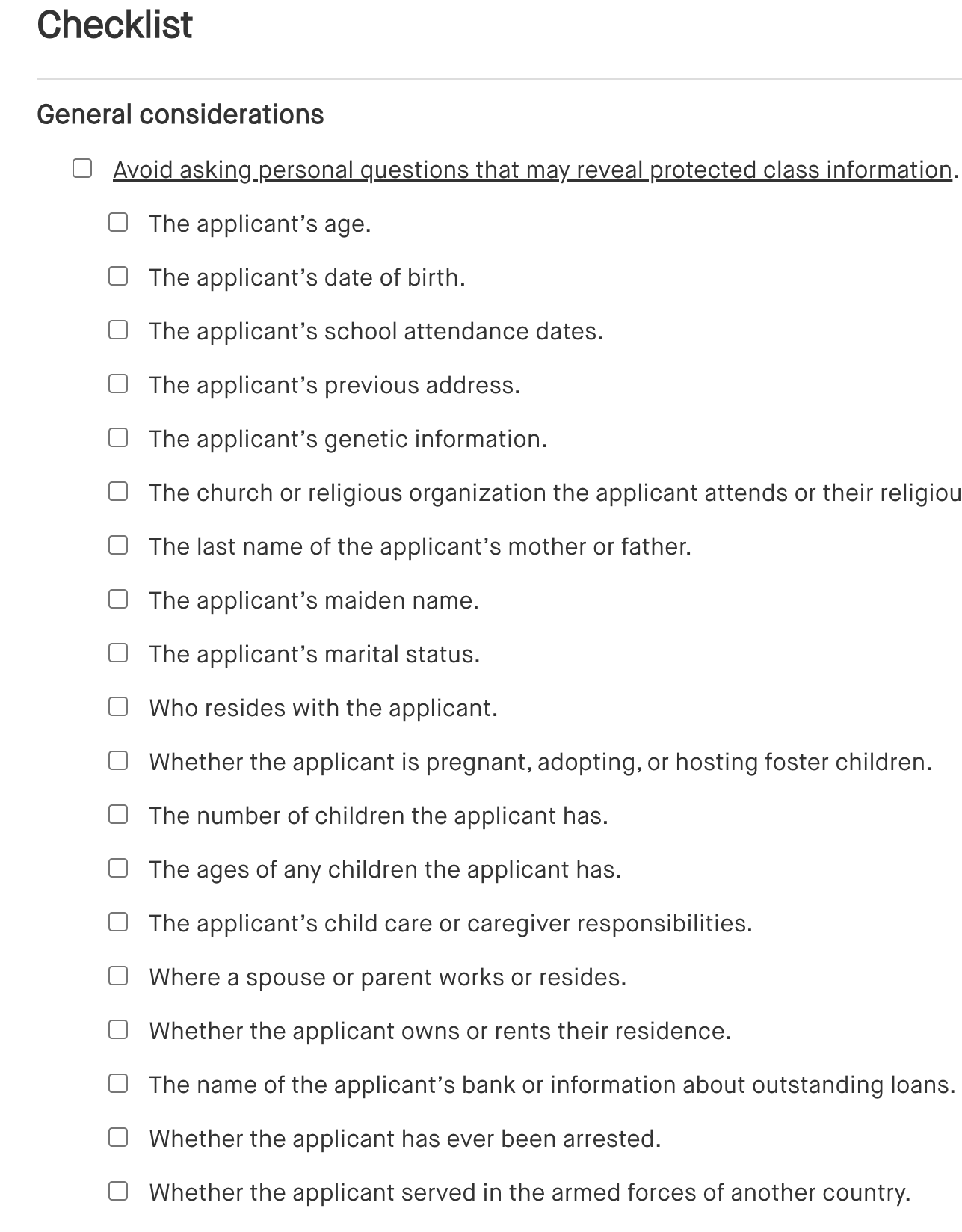
Lists common interview questions to avoid, focusing on those that may unintentionally discriminate based on race, gender, age, or other protected characteristics.