Employee misconduct on social media: Free checklist
Identifies steps for addressing employee misconduct on social media, including reviewing the content, assessing impact, and determining appropriate disciplinary action.
View templateFind free, customizable checklists for managing business processes. Download, tailor, and implement them instantly. Use the search bar below to find a specific checklist or explore the full collection.
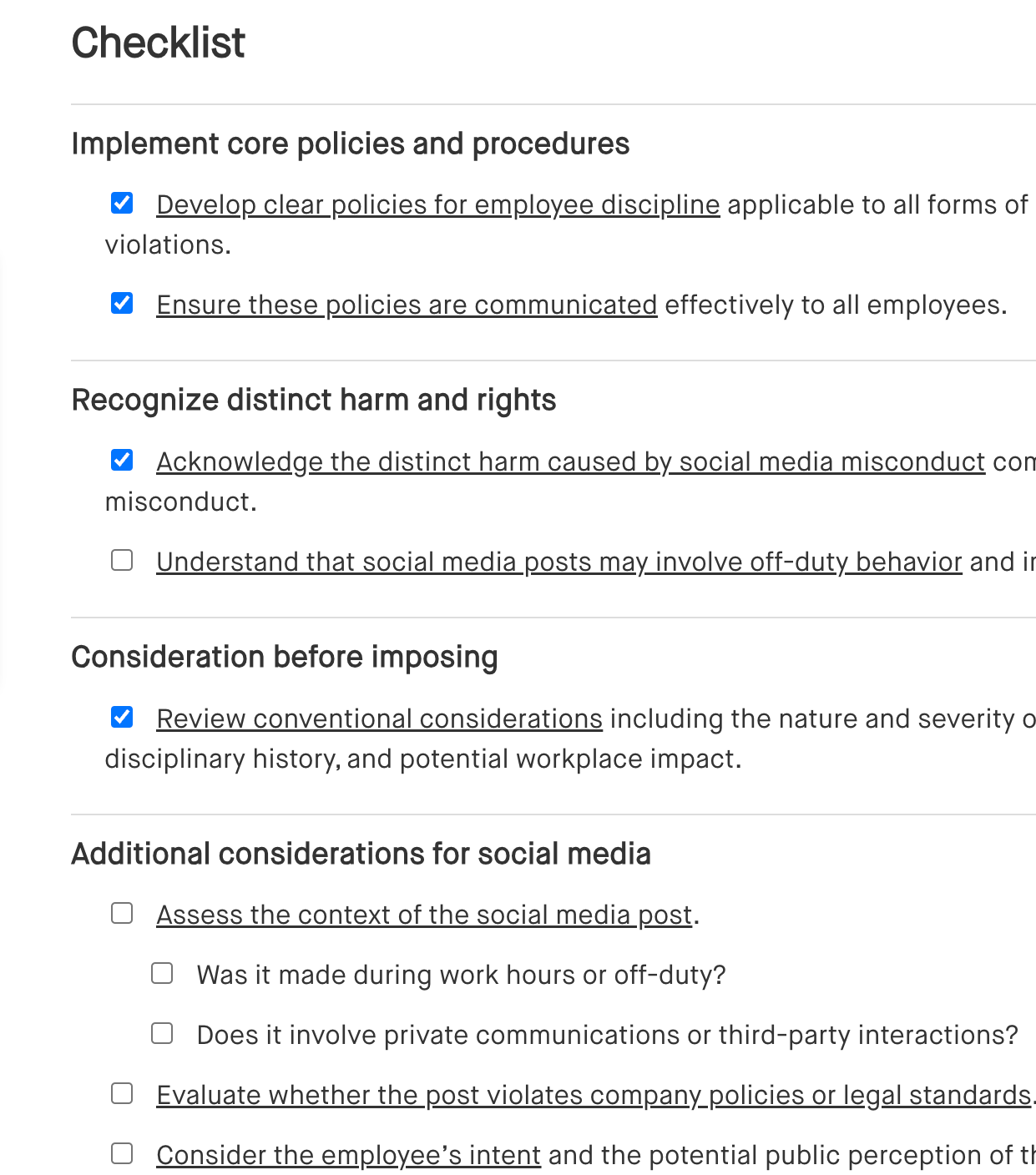
Identifies steps for addressing employee misconduct on social media, including reviewing the content, assessing impact, and determining appropriate disciplinary action.
View template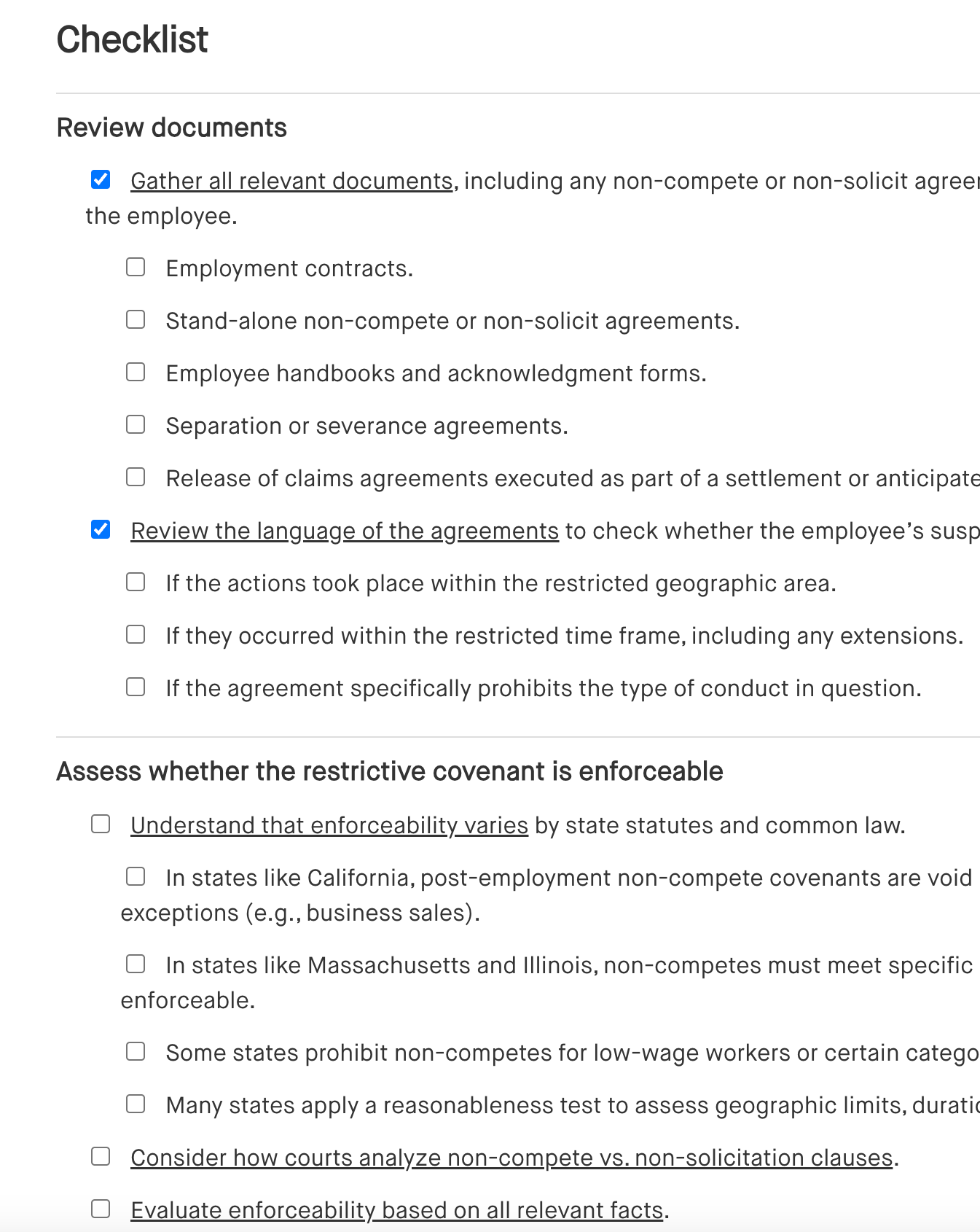
Outlines steps for addressing a non-compete or non-solicitation violation, including reviewing the agreement, investigating the breach, and determining corrective actions or legal steps.
View template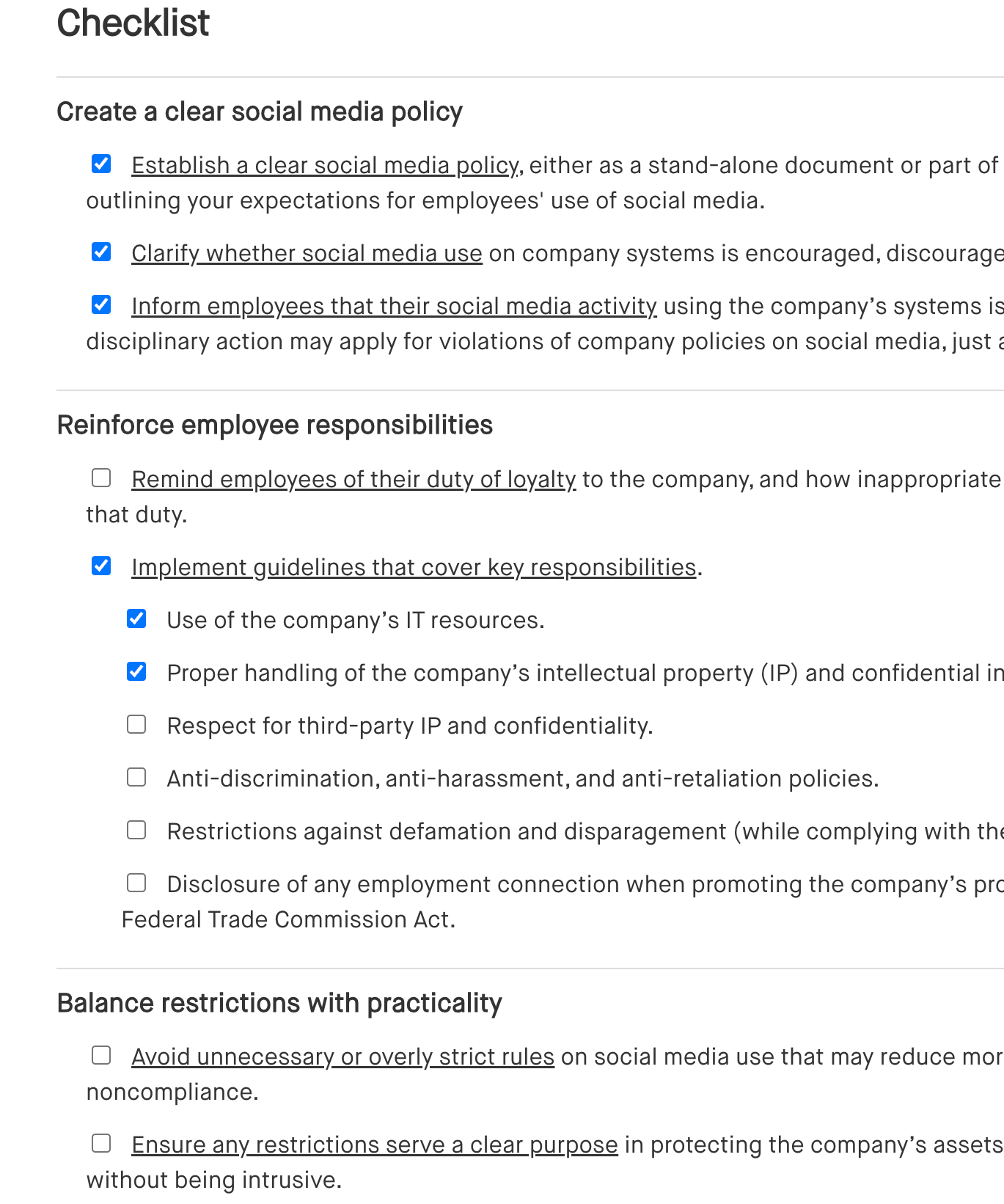
Outlines guidelines for employee use of social media, including setting clear boundaries, monitoring activity, and ensuring alignment with company values and policies.
View template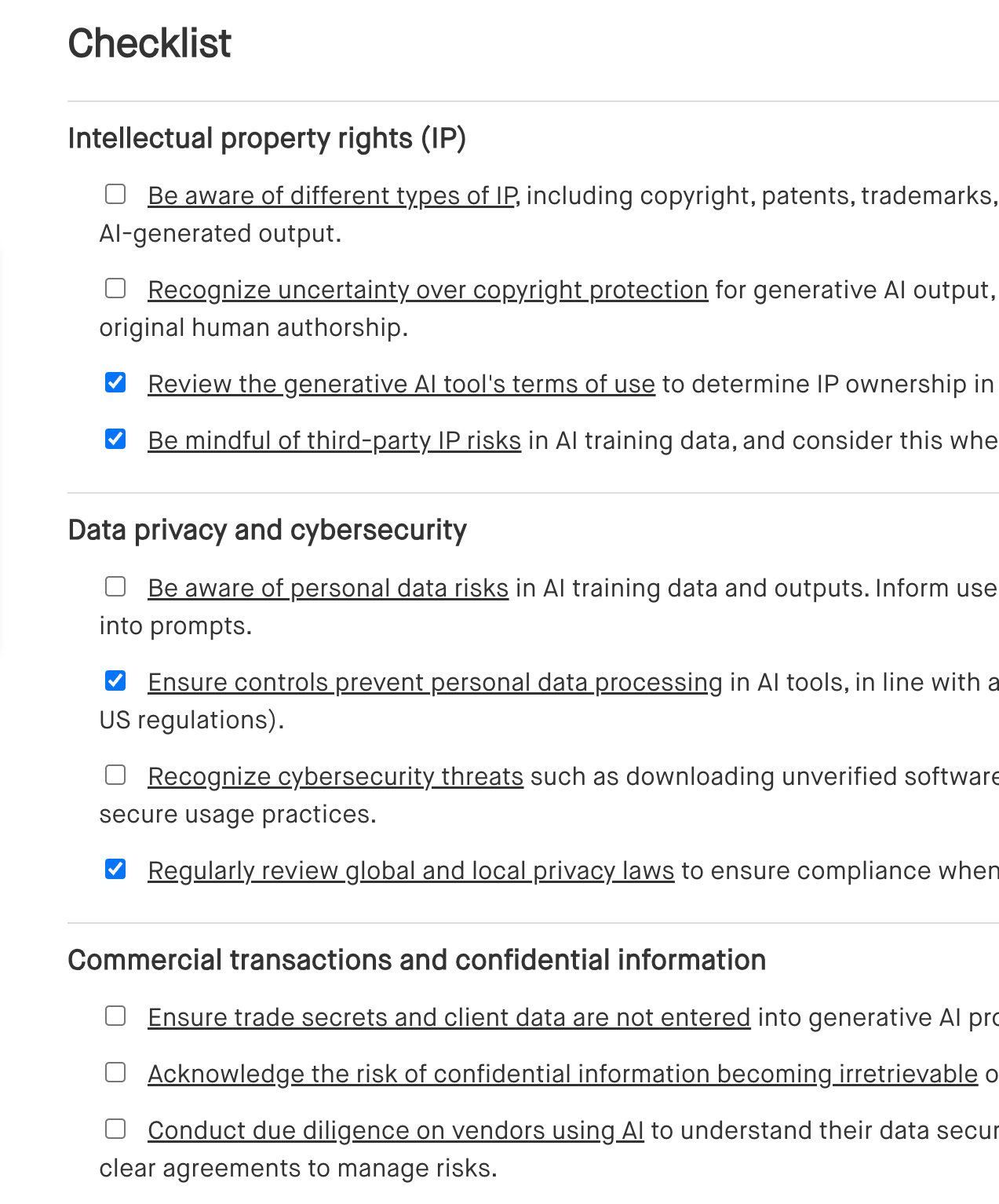
Lists key considerations for using generative AI in the workplace, including data privacy, ethical guidelines, employee training, and potential impact on productivity.
View template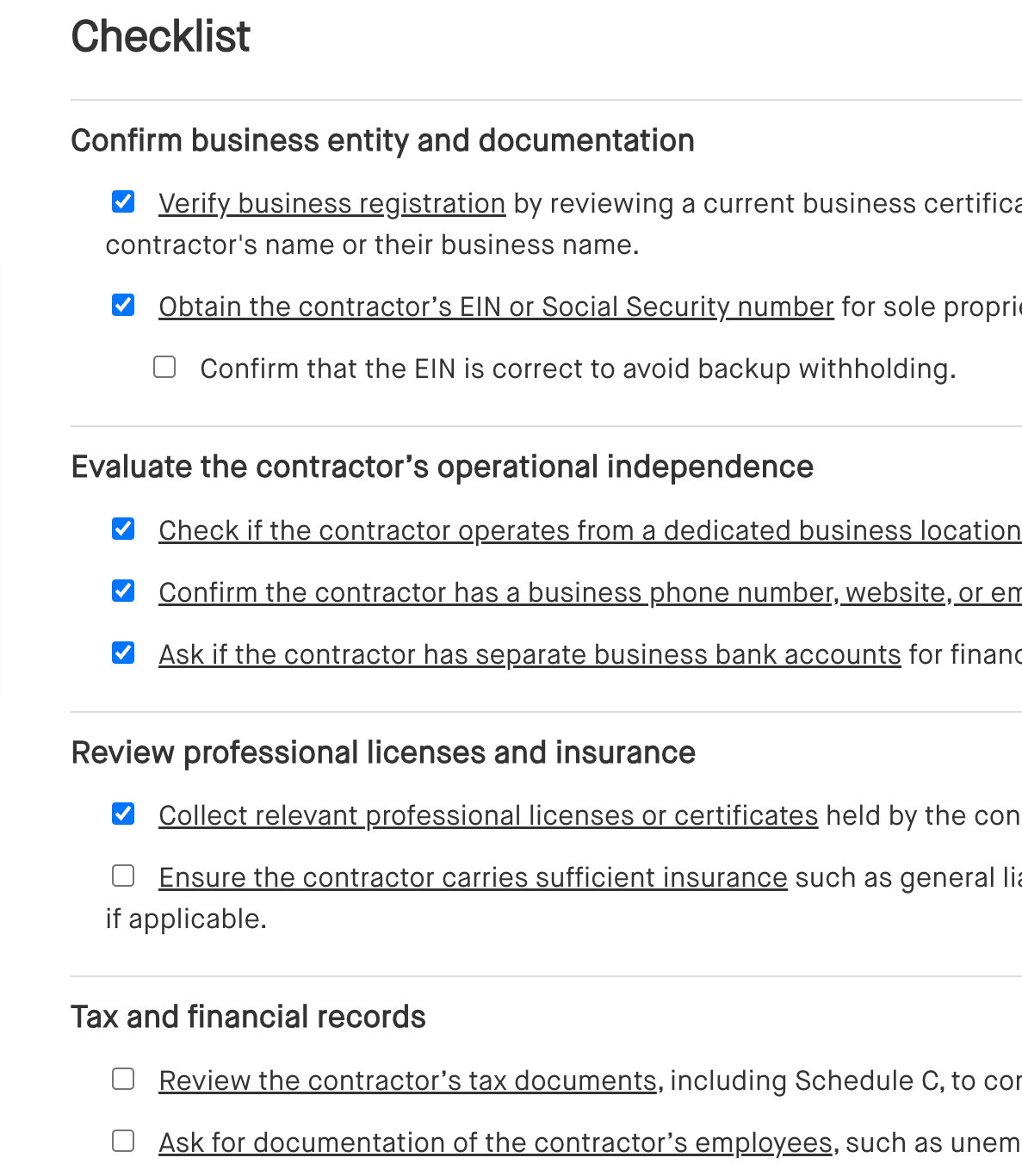
Outlines the steps for hiring an independent contractor, including defining the scope of work, agreeing on payment terms, and achieving compliance with tax and legal requirements.
View template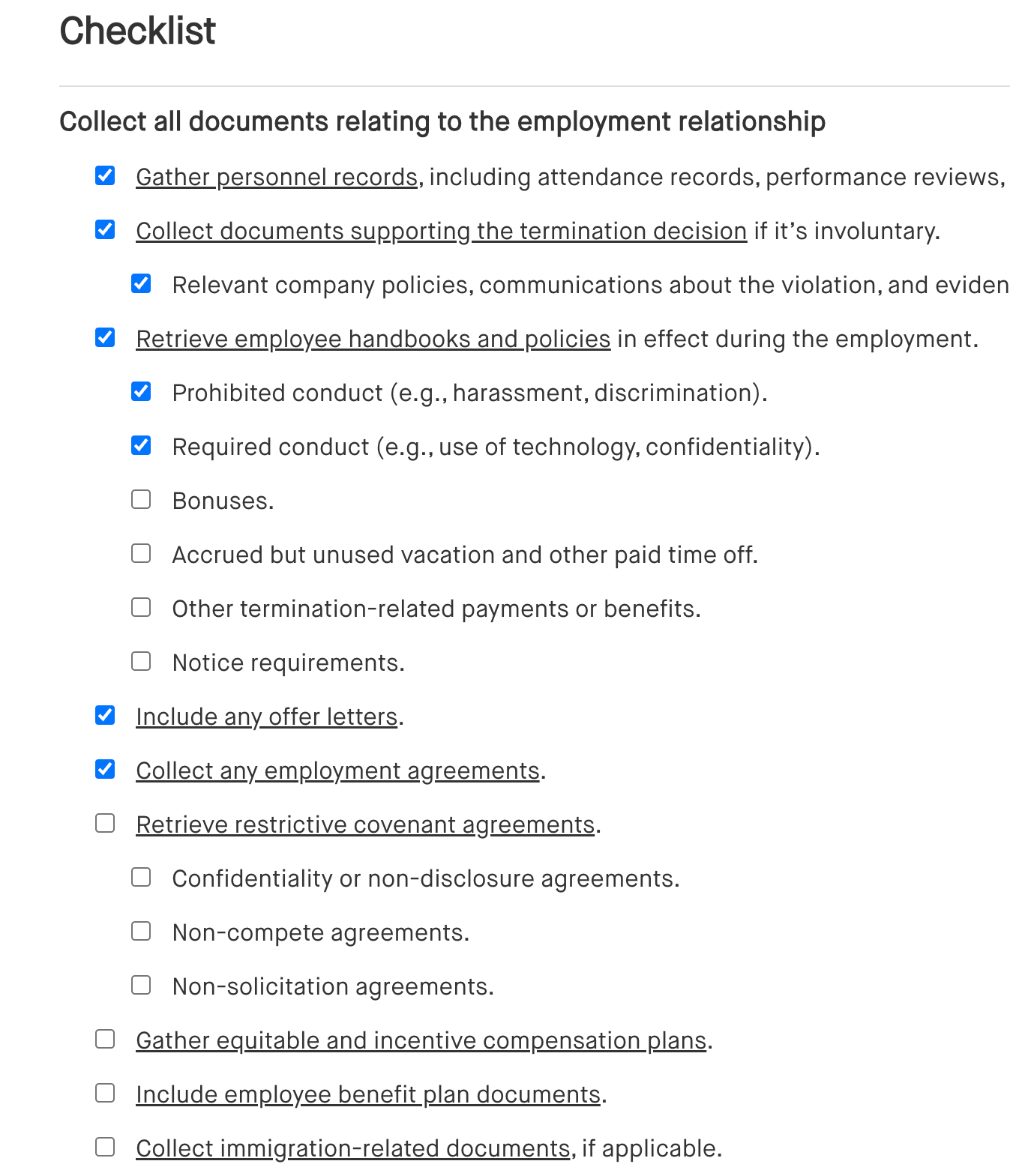
Lists essential steps when handling a departing employee, including exit interviews, return of company property, final paycheck, and updating access permissions.
View template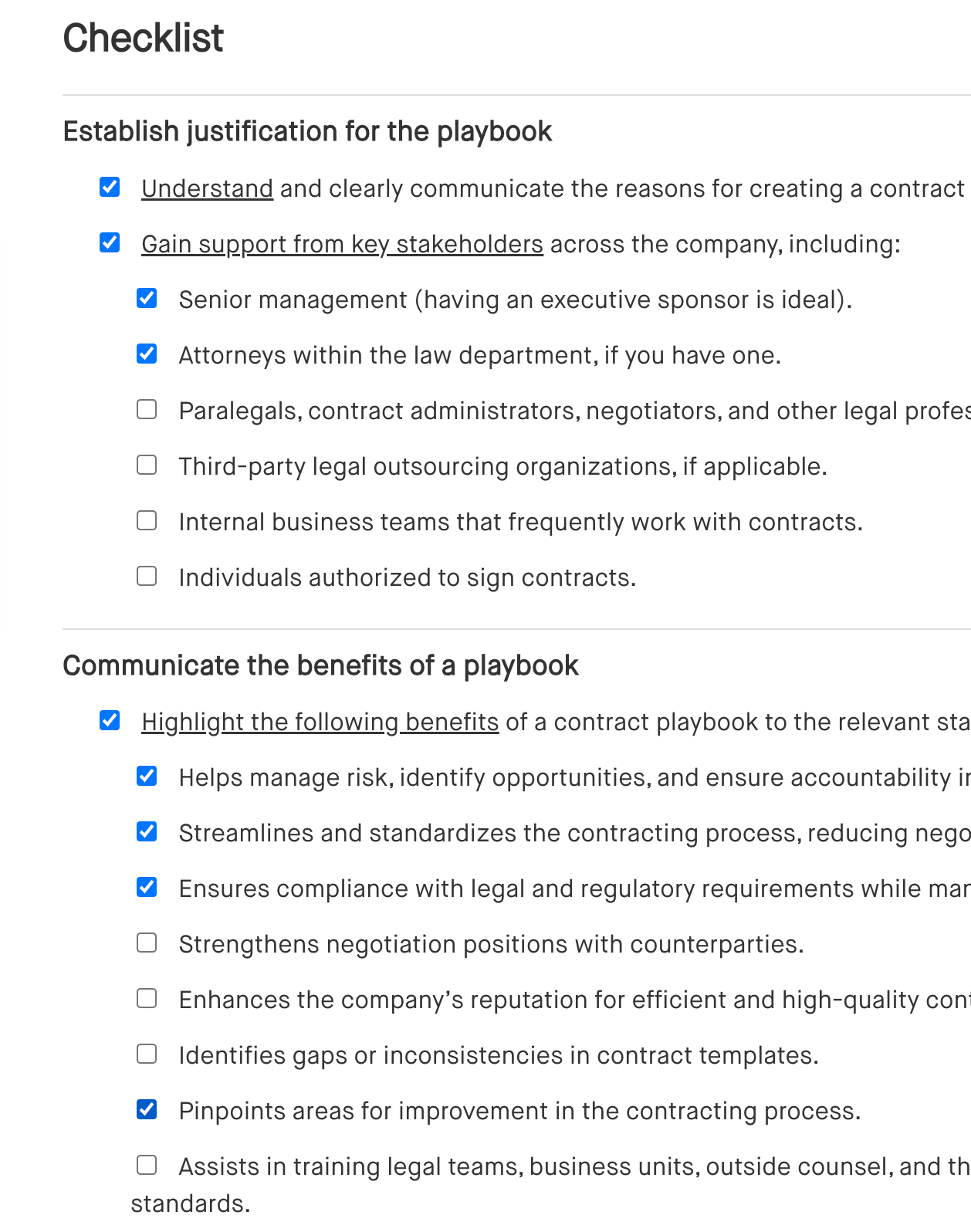
Outlines key elements for creating a contract playbook, including standard clauses, approval workflows, risk management guidelines, and templates for common contract types.
View template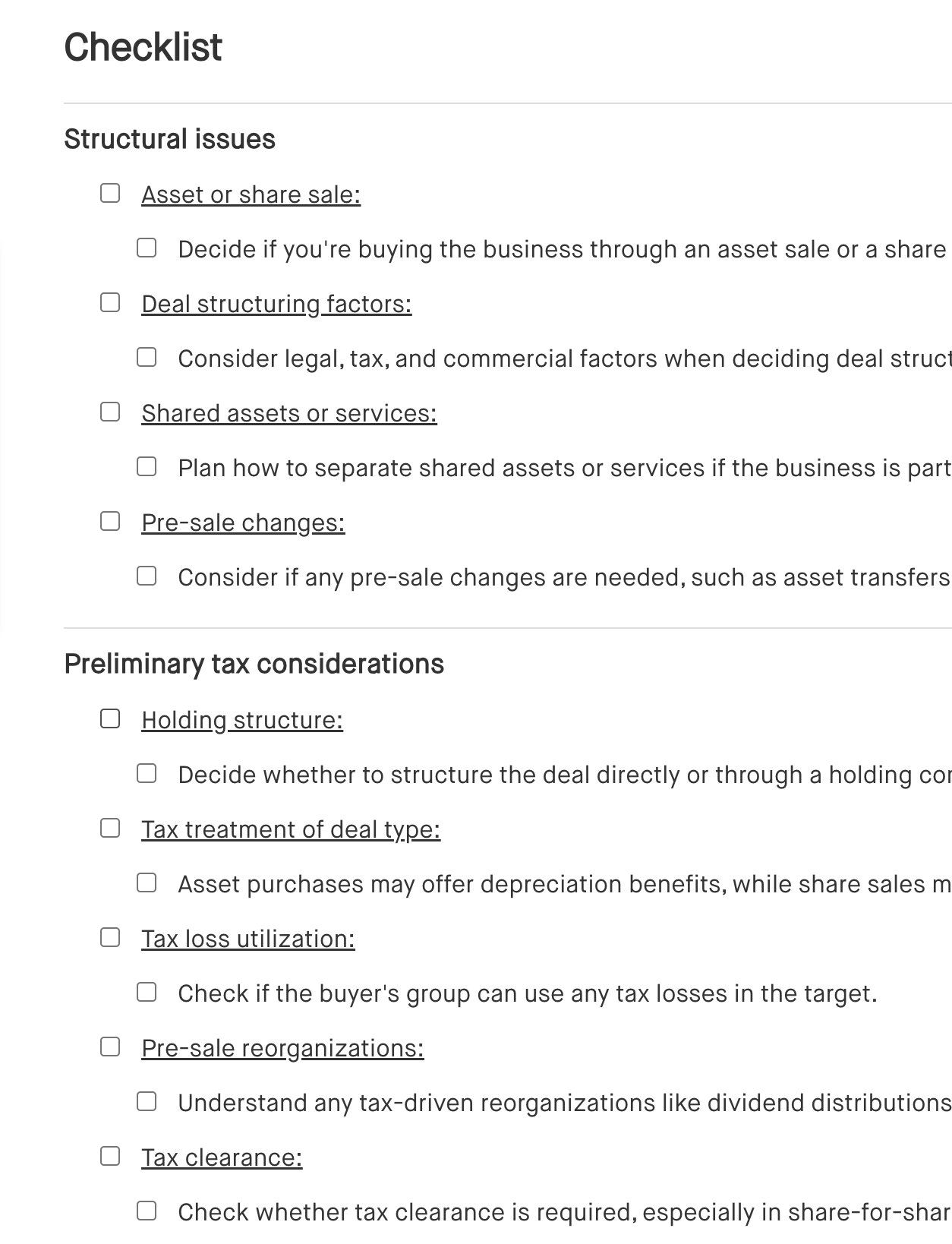
Details the essential steps for a business acquisition, including due diligence, valuation, negotiation, integration planning, and legal documentation.
View template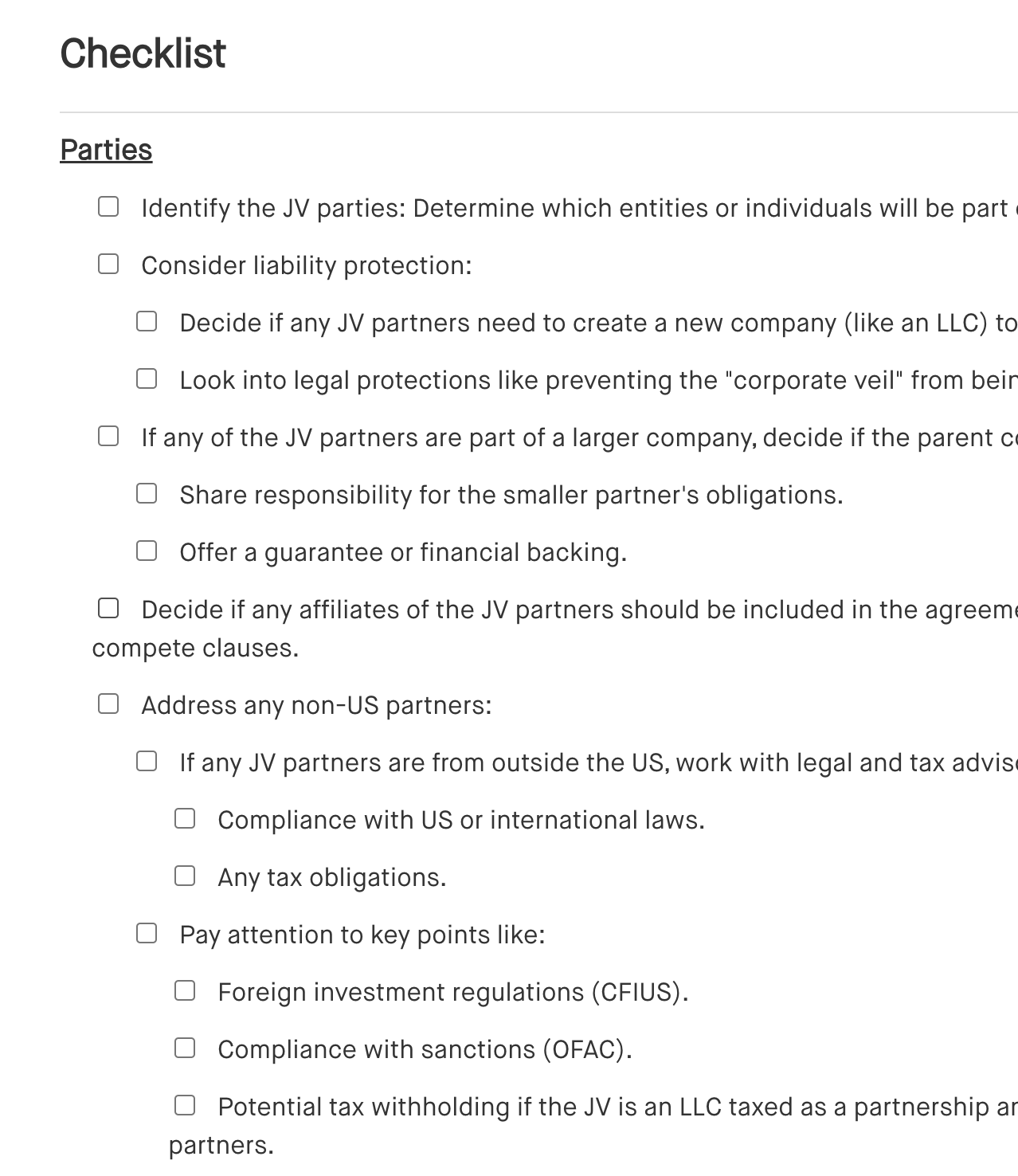
Outlines the steps for forming a joint venture, including defining objectives, selecting partners, drafting agreements, and establishing governance and operational structures.
View template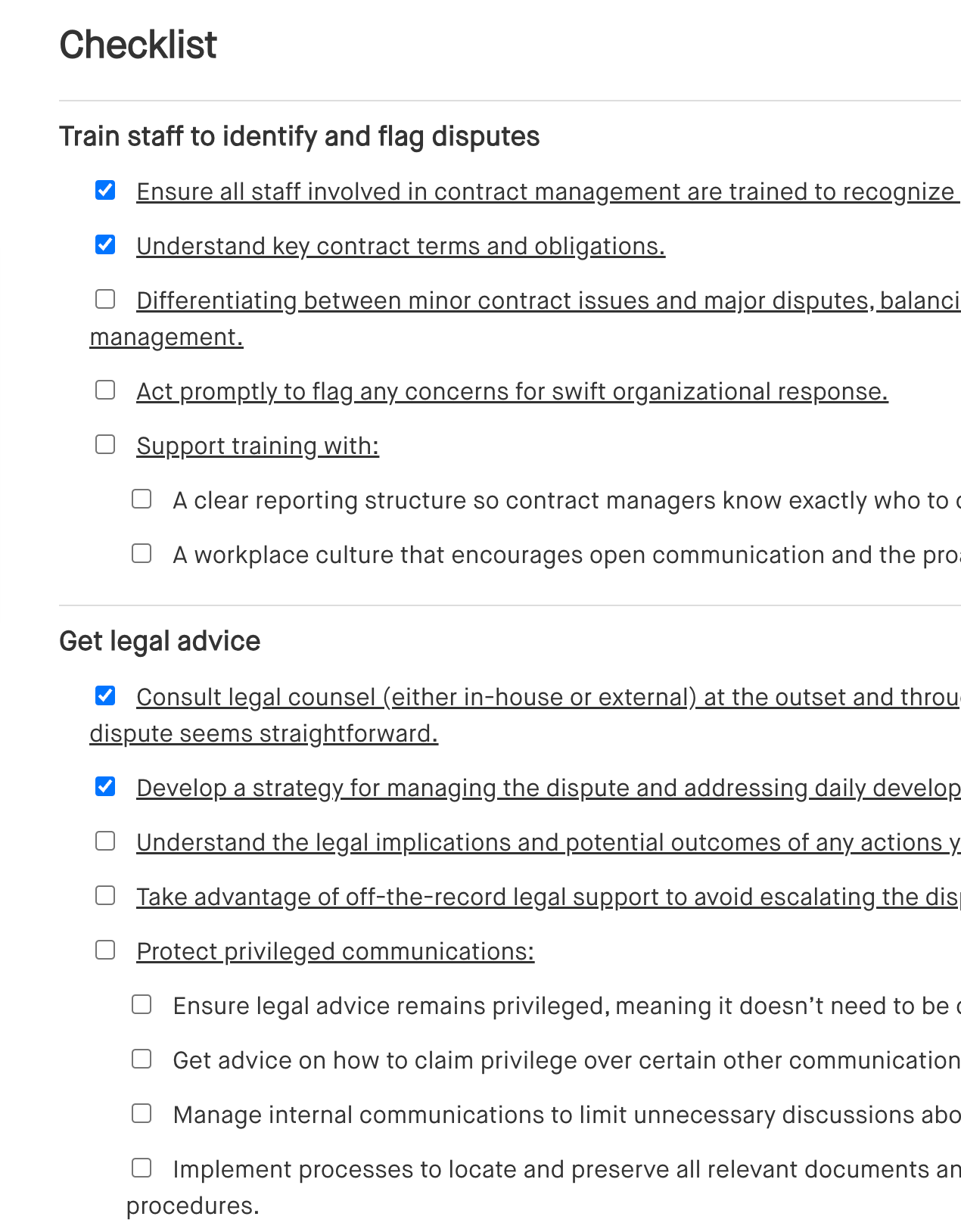
Lists key steps for managing a contract dispute, including reviewing the contract, documenting the issue, communicating with the other party, and considering legal action or alternative dispute resolution methods.
View template